system access
|
Patent Electronic System Access Document Authentication Process
The USPTO.gov account is part of the MyUSPTO single sign-on system. This means that a user only needs to sign in one time to access any of the services |
|
System Access Review Training Guide
They provide assurance that the appropriate users have access to financial systems. To improve the effectiveness of this control certain changes will be. |
|
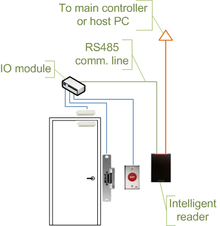
IT ACCESS CONTROL AND USER ACCESS MANAGEMENT
19 Apr 2022 “System or Application Accounts” are user ID's created on IT systems or applications which are associated with specific access privileges on ... |
|
UHS Finance System Access Form
UHS Finance System Access Form. May 2016. UH Mail Code: Last Name: First Name: Middle Initial: Campus Phone: Job Title: Financial Access. College/Division:. |
|
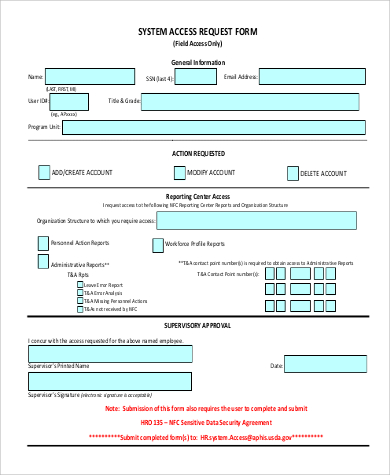
DD Form 2875 SYSTEM AUTHORIZATION ACCESS REQUEST
SYSTEM AUTHORIZATION ACCESS REQUEST (SAAR). OMB No. 0704-0630. OMB approval expires: 20250531. The public reporting burden for this collection of |
|
UHS Finance System Access Form
UHS Finance System Access Form. October 2006. UH Mail Code: Last Name: First Name: Middle Initial: Campus Phone: Job Title: Financial Access. |
|
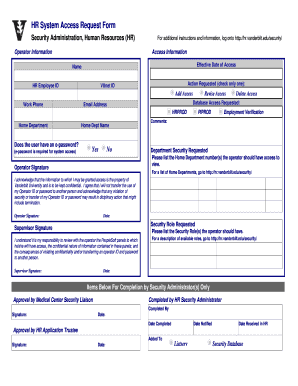
HR System Access Request Form
User Agreement. I understand that the data contained in the Human Resource Management System is confidential. I also understand that the access I. |
|
Sap learning hub and sap learning system access supplemental
services (“Agreement”) between SAP and Customer and apply solely to SAP Learning Hub and SAP. Learning System Access (the “Cloud Service”). |
|
Application for system access
Application for system access. We the undersigned |
|
UM System Access
ACCESS TO UM SYSTEMS. SiswaMail FAQs. 1 What is my student email address? 2 How to log in into SiswaMail? SiswaMail is now accessible via Gmail (gmail.com). |
|
System Access Review Guideline - University of California
System Access Review Guideline - University of California |
|
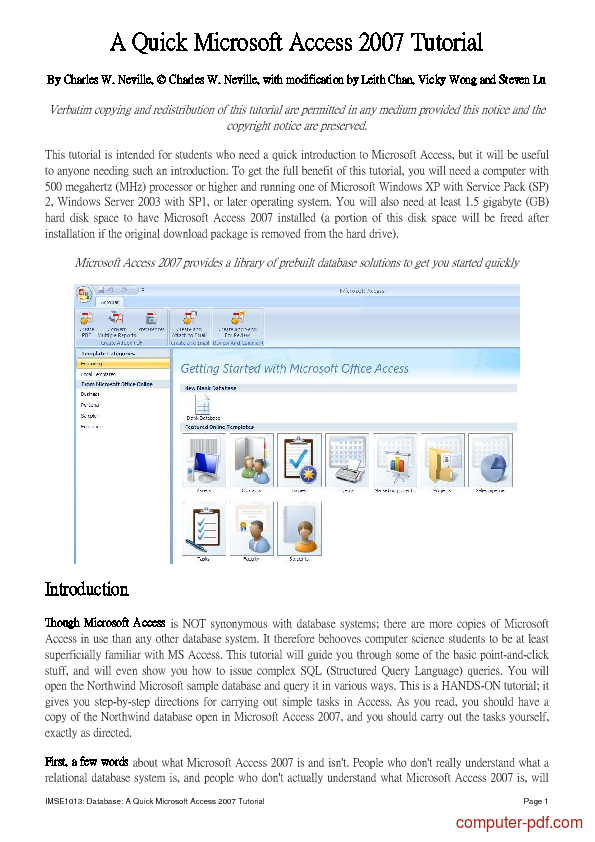
INTRODUCTION TO MICROSOFT ACCESS - University of Michigan
Microsoft Access is a relational database application that is composed of four main objects: Tables: for storing data Queries: for viewing data Forms: for entering data Reports: for printing data When you launch Access your database window shows the different objects available to you on the left and |
|
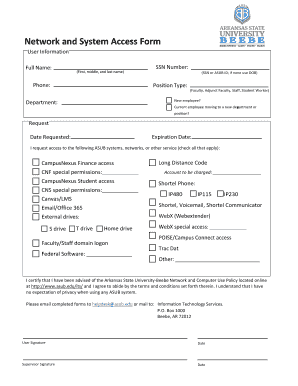
System Access Request Form - San José State University
System Access Request Gaining Access To gain access to PeopleSoft or its associated systems an employee must successfully complete the appropriate CMS training This form must be completed and signed by the employee and the employee’s manager then sent to the CMS Security Group (zip 0042) |
Product Highlights
Choose from one of several configurations to fit your needs
Product Description
As a blind or visually impaired consumer, you want reliability wrapped up into one easy-to-use package. With Serotek you can rely on a simple interface and extensive help documentation to let you hit the ground running. We understand the hassles of learning a new product and do everything we can to make your transition as seamless as possible. Best...
What is system access?
Whether you’re composing a document or spreadsheet, keeping track of appointments, sending e-mail, or surfing the web, System Access provides intuitive access to your Windows environment. For work or pleasure, System Access gives you what you need to make the most of your computer without draining your patience. Download it now!
What is a system access review?
The System Access Review consists of three main roles: 1. Inquire - Read-only access; users cannot make changes or updates to the data on the page. 2. Review - Allows the user to confirm system access. 3. Approve - Allows the user to confirm system access and sign off that the review is complete. Only DFLs will have the ‘Approve’ role.
What are the formal procedures for user access management?
User Access Management Formal procedures should be in place to control the allocation of access rights to information systems and services.
What is application and information access control?
Application and Information Access Control Security facilities should be used to restrict access to and within application syste ms. Logical access to application software and information should be restricted to authorized users. Application systems should:
|
The System Access Manager is an account management module
System Access Managerfor GLP FDA 21 CFR part 11 compliance Manages unique electronic signatures in line with the principles set down by the FDA and |
|
SYSTEM ACCESS REVOCATION - Coloradogov
This Request can only be used for those third party users who already have access to DOHCPF systems “Revocation״ means ALL system access privileges will |
|
Colleague ERP System Access and Security Policy
It applies not only to stored information but also to the use of the various computer systems and programs used to generate or access data, the computers that run |
|
INFORMATION SYSTEM ACCESS
INFORMATION SYSTEM ACCESS AUTHORIZATION AND BRIEFING FORM Printed Name: Phone: I have the necessary clearance for access to the following |
|
HLS System Access Request Form - Harvard University
This form is required for access to sensitive data systems The authorized business owner of a system must approve access before account requests are |
|
Request for system access
REQUEST FOR SYSTEM ACCESS EMPLOYEE/USER TYPE OF ACCESS REQUESTED Action Requested: TYPE OF SYSTEMS REQUESTED Network |
|
FINANCE SYSTEM ACCESS REQUEST
FINANCE SYSTEM ACCESS REQUEST > Complete lines 1 - 8 > Obtain approval signature (line 8) and email form to UMSL Accounting Services |



![PDF] A Quick Microsoft Access 2007 free tutorial for Beginners PDF] A Quick Microsoft Access 2007 free tutorial for Beginners](https://img.yumpu.com/37092540/1/500x640/it-security-procedure-pdf-112-kb-west-coast-district-health-board.jpg)
![IT Security Procedure [PDF 112 KB] - West Coast District Health Board IT Security Procedure [PDF 112 KB] - West Coast District Health Board](https://zbook.org/img/2011/planning-and-system-manual-access-professional-issue-2020-210005937-02-en.jpg)