twos complement exploit
|
Twos Complement
This is the two's complement representation of the negative integer. EXAMPLE: Find the two's complement of -17. Step 1: 1710 = 0001 00012. Step 2: Take |
|
12-Bit Octal Ultralow Glitch Voltage Output DAC datasheet (Rev. A)
twos complement (BTC) input data formats. Format in Table 2. selection is done by the RSTSEL pin. If the RSTSEL is kept low the 12-bit input data is |
|
All optical four bit twos complement generator and single bit
Different all optical logic gates functional devices |
|
EECS 452 – Lecture 3
When can an overflow occur in 2's complement? Let #1 and #2 be two N-bit 2's complement numbers A filter design could exploit the two's complement overflow. |
|
High-Avidity CTL Exploit Two Complementary Mechanisms to
Thus we conclude that high-avidity CTL exploit two complementary mechanisms that combine to prevent the spread of virus within the animal: earlier |
|
Nonlinear parallel-in-time schur complement solvers for ordinary
19 сент. 2017 г. idea of a global linearization of nonlinear ODEs to exploit time-parallelism is not new. ... 2) Schur complement solve are shown. Out of the plots ... |
|
Exploiting Narrow Bitwidth Operations for Low Power Embedded
1 two input operands |
|
All optical four bit twos complement generator and single bit
Different all optical logic gates functional devices |
|
Practical Firmware Reversing and Exploit Development for AVR
V – two's complement oVerflow indicator. S – N ⊕ V for Signed tests. H – Half carry flag. T – Transfer bit (BLD/BST). I – global Interrupt enable/disable flag |
|
Undefined Behavior: What Happened to My Code?
tions that exploit undefined behavior. One reason for these For example -fno-strict-overflow in GCC does not fully enforce two's complement on signed. |
|
Secure Coding in C and C++
A software vulnerability may result when a program evaluates an integer to an unexpected value. In two's complement arithmetic a signed integer ranges. |
|
FLInt: Exploiting Floating Point Enabled Integer Arithmetic for
9 ?.?. 2565 FLInt: A two's complement and logic operation based comparison operator for floating point numbers where we formally prove the correctness ... |
|
Outer surface lipoproteins from the Lyme disease spirochete exploit
18 ?.?. 2565 complex termed the first component of complement C1 |
|
ACGNet: Action Complement Graph Network for Weakly-supervised
incurs two critical issues that greatly limit localization per- formance. On the one hand tates an action segment to exploit complementary clues from. |
|
A New High Radix-2r (r 8) Multibit Recoding Algorithm for Large
11 ?.?. 2556 radix-2r two's complement multiplication for any value of r. ... architecture so that maximum parallelism is exploited. As. |
|
Resilience and Vulnerability: Complementary or Conflicting Concepts?
Resilience and vulnerability represent two related yet different approaches to understanding the response of systems and actors to change; to shocks and |
|
Exploiting Narrow Bitwidth Operations for Low Power Embedded
two's complement representation is sign extension. Due to sign extension an arithmetic operation for narrow bitwidth operands requires the dynamic power |
|
Generating Complement Data for Aspect Term Extraction with GPT-2
14 ?.?. 2565 we propose a novel method to better exploit the available labeled data for ATE by comput- ing effective complement sentences to augment. |
|
Energy-efficient Dense DNN Acceleration with Signed Bit-slice
15 ??.?. 2565 accelerates both high-precision and dense DNNs by exploiting ... to 2's complement data and it cannot exploit the benefits of. |
|
Complementary Resources and the Exploitation of Technological
1 ?.?. 2546 Firm size may be a critical determinant in choosing an innovation mode. When two or more firms are involved Williamson (1975) hypothesized that ... |
|
Twos omplement Review - University of California Berkeley
exploit underlying features of the architecture – memory management special instructions parallelism 6/21/2011 Spring 2011 -- Lecture #3 11 Compilation: Disadvantages •Compiled files including the executable are architecture-specific depending on CPU type and the operating system •Executable must be rebuilt on each new system |
|
Understanding n's Complement HackerEarth
GVSU School of Computing - Grand Valley State University |
|
2’s Complement and Floating-Point - University of Washington
Understanding Two’s Complement • An easier way to find the decimal value of a two’s complement number: ~x + 1 = -x • We can rewrite this as x = ~(-x -1) i e subtract 1 from the given number and flip the bits to get the positive portion of the number • Example: 0b11010110 • Subtract 1: 0b11010110-1 = 0b11010101 |
|
006-twos-complement - University of Illinois Urbana-Champaign
Distinguish 2’s Complement from Negation Here or elsewhere you will hear the phrase “take the 2’s complement ” We will try not to use “2’s complement” in that way Students get confused between the 2’s complement representation for signed integers and the operation of negation on a bit pattern for a number represented with |
|
Two’s Complement - Rochester Institute of Technology
Step 1: Write the absolute value of the given number in binary form Prefix this number with 0 indicate that it is positive Step 2: Take the complement of each bit by changing zeroes to ones and ones to zero Step 3: Add 1 to your result This is the two’s complement representation of the negative integer EXAMPLE: Find the two’s complement of 17 |
|
Searches related to twos complement exploit PDF
two’s complement discussed next purpose TakingtheTwo’sComplement Therearetwoprocessesfortakingthetwo’scomplementofanumber Theonethat studentsfindthemostnaturalinvolvesfirsttakingtheone’scomplementandthenadding tothatcomplement Wemustthencovertheadditionoftwobinarybitsspecificallymentioningeachofthe |
What is the 2's complement?
The 2’s complement is just the same as above with the only difference being in the count of binary numbers : 0000 , 0001 , 0010 , 0011 , 0100 , 0101 ….and so on. (+ve) and 1111 , 1110 , 1101 , 1100 …and so on (-ve). Now for sake of uniformity we use all numbers starting with MSB 1 as negetive.
What is the decimal value of a two's complement number?
An n-bit, two’s complement number can represent the range [?2 ?1, 2 ?1? 1]. Note the asymmetry of this range about 0 –there’s one more negative number than positive An easier way to find the decimal value of a two’s complement number:
How can a 4-bit two's complement operation be implemented?
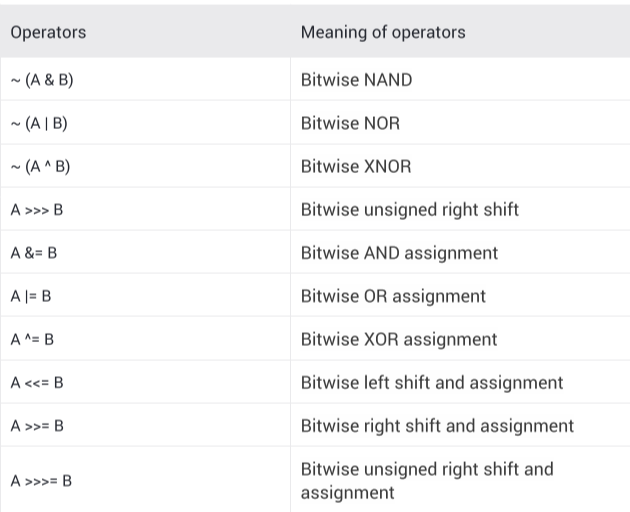
How can a 4-bit two's complement operation be implemented using only boolean logic gates (AND, OR, NOR, NOT, NAND, XOR, and XNOR)? A two's complement operation is simply a one's complement operation followed by the addition of 1 to the result. One's complement is easy: simply invert all of the input bits.
What is one's complement arithmetic?
One’s–complement arithmetic is that arithmetic that uses the one’s–complement ofa binary integer to represent its negative. 100 in8–bitone’s complement. 0110 0100. 100 in 8–bit one’s complement.
|
Twos Complement
Step 1: Write the absolute value of the given number in binary form Prefix this number with 0 indicate that it is positive Step 2: Take the complement of each bit |
|
EECS 452 – Lecture 3 - Eecs Umich
A filter design could exploit the two's complement overflow resiliency For example: consider an FIR filter having an equal number of positive and negative |
|
Secure Coding in C and C++
A software vulnerability may result when a program evaluates an integer to an In two's complement arithmetic, a signed integer ranges from -2n-1 through |
|
Chapter 6 - School of Computer Science - Carleton University
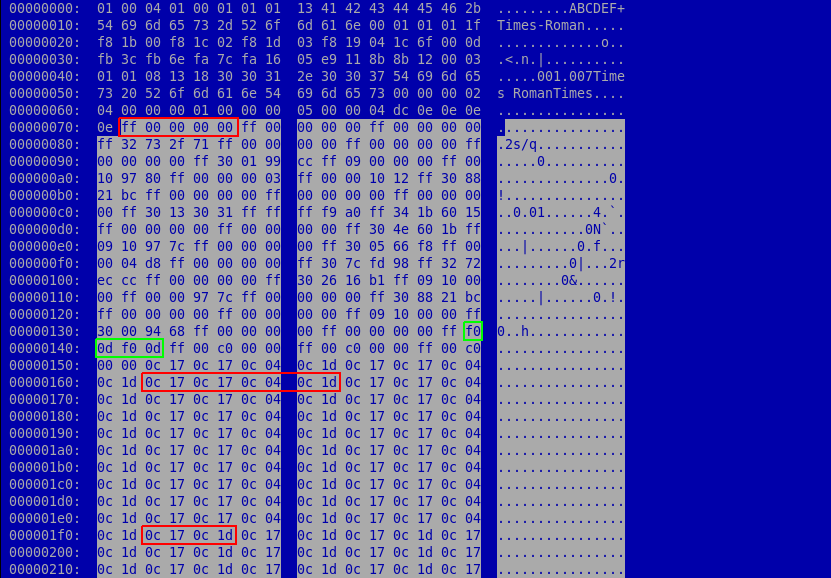
25 sept 2019 · 6 6 Buffer overflow exploit defenses and adoption barriers The C99 standard added exact-length signed (two's complement) integer types: |
|
Secure Coding in C++: Integers - SEI Digital Library - Carnegie
Two's Complement The two's complement form of a negative integer is created by adding one to the Based on a real-world vulnerability in the handling of |
|
2s complement integers
- 128 128 -> 0 • We can get round this problem by a clever trick that exploits integer overflow (Slide 3), giving Page 5 9 CSCU9V4 Systems Two's complement |
|
Integer overflow - Stephen Checkoway
Buffer overflow vulnerability-finding strategy 1 Look for the Exploiting integer overflow Two's complement integers don't model mathematical integers well |
|
A Understanding Integer Overflow in C/C++1 - wdtz / Will Dietz
integers on all modern platforms use a two's complement representation where the value A C or C++ compiler may exploit undefined behavior in optimizations |
|
COMPSCI 210 S1 C 2013 - School of Computer Science - The
4 avr 2013 · Convert the following decimal integers to (1) 16-bit 2'S complement representation and can be exploited to reduce the logic: for any row that |

![PDF] The use of reduced two's-complement representation in low PDF] The use of reduced two's-complement representation in low](https://d3i71xaburhd42.cloudfront.net/5ca28a7a1fea560512ff4b0c79abc6469af8c483/2-Figure3-1.png)
![PDF] The use of reduced two's-complement representation in low PDF] The use of reduced two's-complement representation in low](https://i1.rgstatic.net/publication/2805523_Combined_Unsigned_and_Two's_Complement_Saturating_Multipliers/links/55a9c8ce08aea3d0868046a8/largepreview.png)







![PDF] The use of reduced two's-complement representation in low PDF] The use of reduced two's-complement representation in low](https://1.bp.blogspot.com/-V8Vw-HnEmEw/Wva2eDuOLKI/AAAAAAAAB_E/epsmrPDM4PIQzsgycY9M6ncQjkPA5SEiQCEwYBhgL/s1600/metasploit%2Bussage%2Bexample%2Breverse%2Bshell.png)


![PDF] The use of reduced two's-complement representation in low PDF] The use of reduced two's-complement representation in low](https://imgv2-1-f.scribdassets.com/img/document/248629184/298x396/9d913fb376/1417274012?v\u003d1)