checkpoint 3 tier architecture pdf
|
Word Template
Point Architecture These objectives and study questions provide a review of 3 Design/troubleshoot OSPF/BGP in GateD and IPSO IPSRD environments 4 |
|
Architecture du Système Oracle 10g
o Connexion Multi Tiers : Dans une architecture multi tiers la machine o Lors de timeouts (environ toutes les 3 secondes par défaut) o Lors d'un checkpoint |
|
Check Point Infinity NGTP Architecture Whitepaper
This document describes how Check Point Next Generation Threat Prevention (NGTP) platforms fulfill the Check Point Infinity goal of keeping businesses |
|
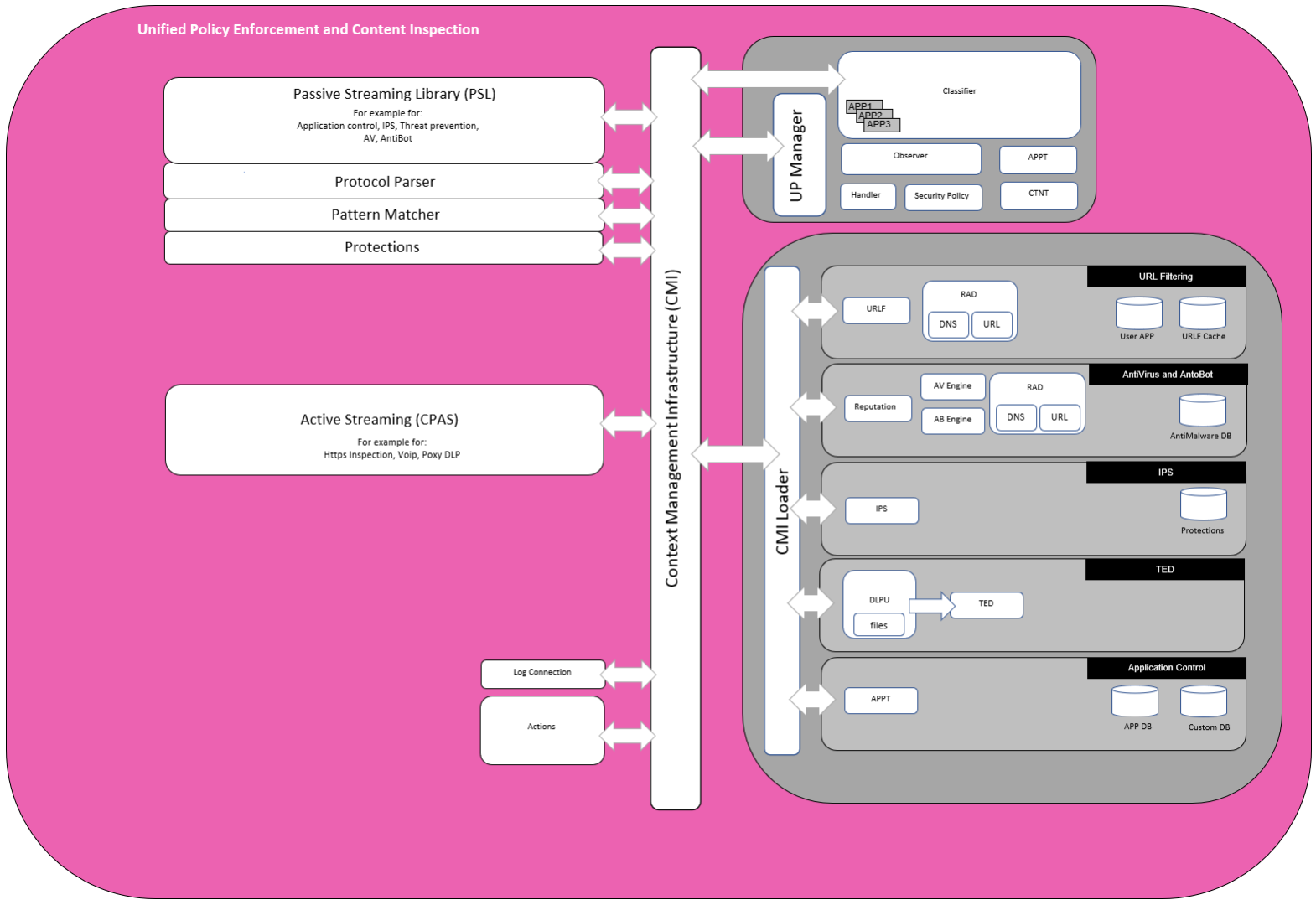
Check Point IPS Engine Architecture:
The engine provides the ability to find regular expressions on a stream of data using a two tiered inspection process The first tier quickly filters out the |
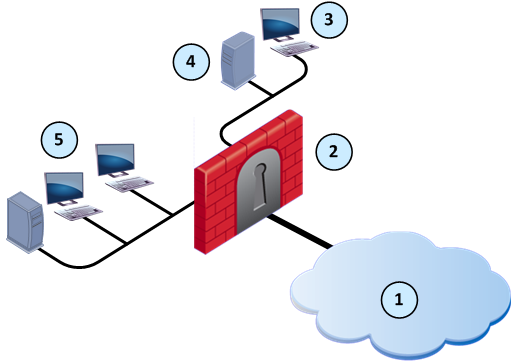
What is checkpoint architecture?
Checkpoint is a Next Generation Firewall which has three basic pillars.
Security Management Server.
Security Gateway (Enforcement Module) SmartConsole.What is 3 tier architecture component of checkpoint firewall?
These Components are:- (.
1) Smart Center Server, (.
2) Security Gateway, and (.
3) Smart Console.
These components can also be understood as roles.
These roles can be placed together or independent to each other.18 juil. 2020Secure Internal Communication (SIC) - Authenticates communication between Security Management Servers, and between Security Gateways and Security Management Servers.
VPN certificates for gateways - Authentication between members of the VPN community, to create the VPN tunnel.
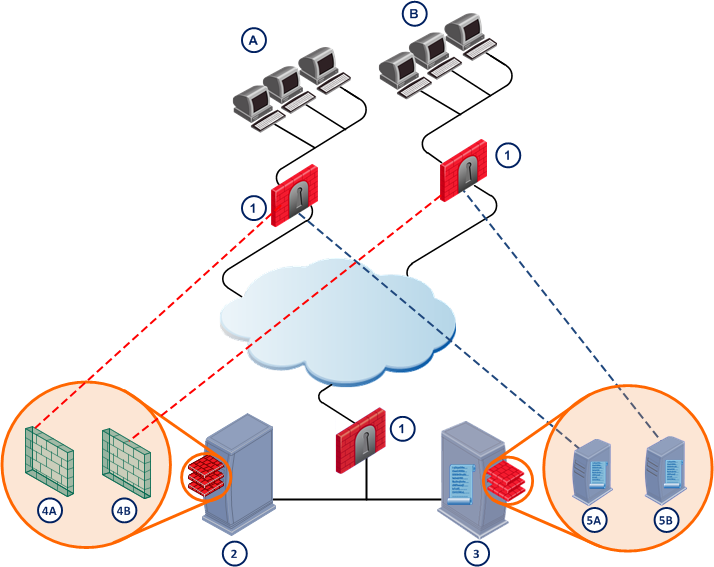
What is a 3 tier firewall architecture?
A three-tier architecture would include three firewalls: one on the outside and two different layers on the inside.
The ISP should have a firewall that restricts all connections to their protected host except those that are absolutely required.
|
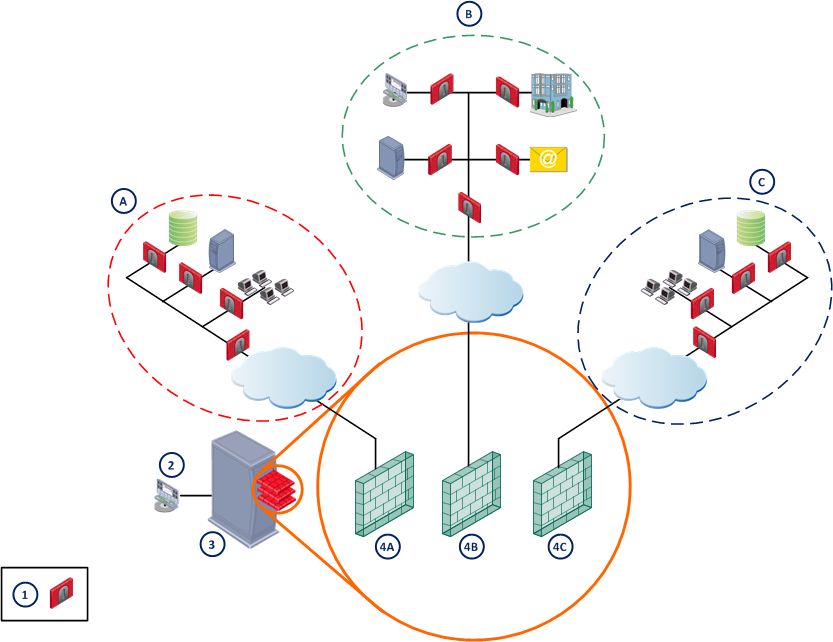
Check Point R80.10 Security Management Architecture Overview
Automation API orchestrates workflows enabling security alignment with IT processes and systems. Page 3. MAIN COMPONENTS OF THE R80.10 SECURITY MANAGEMENT |
|
Brochure
20-Apr-2021 Our security management package combines policy management monitoring and event management in one platform. UNIFIED. SIMPLE. Page 3. ©2021 ... |
|
Check Point IPS Engine Architecture: - New Technologies Provide a
Pattern matching is done via a two tiered inspection. The first tier quickly filters out about 90% of the malicious traffic. Adding additional signatures on the |
|
Check Point Security Appliance Brochure
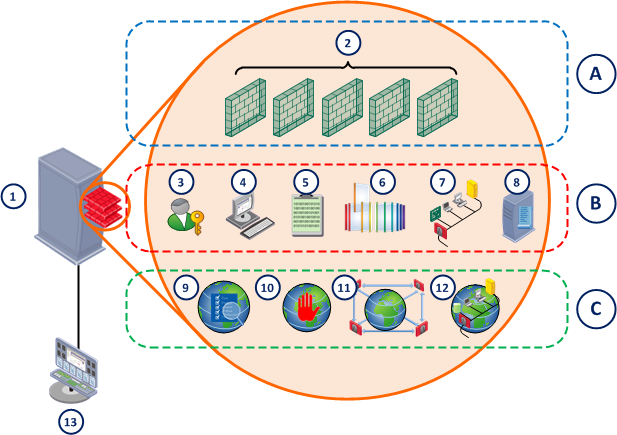
It's time to step up to Gen VI of cyber security with the architecture that system (800 Gbps per single gateway) |
|
Checkpoint L2 Training
Checkpoint Architecture. Checkpoint provides a three-tier model that consists of the following components: ?SmartCenter server /Dashboard. |
|
Check Point Learning & Training - Certification Program Model FAQ
This core 3-day technical certification course provides an understanding of basic Point Infinity Cyber Security Architecture. |
|
Maestro-hyperscale-orchestrator-datasheet.pdf
2022 Check Point Software Technologies Ltd. All rights reserved. [Protected] |
|
CloudGuard for OCI Reference Architecture
The following diagram illustrates this reference architecture: Page 3 Check Point CloudGuard Network Security's multi-layered threat prevention ... |
|
Checkpoint-secure-cloud-transformation.pdf
As a prerequisite you should be well versed in cloud and security design concepts and generic security architectural concepts and framework. Page 3. 1. © June |
|
Check Point
3. The legacy approach . CloudGuard SaaS architecture . ... 3) Sharing threat intelligence with a cloud-based platform allows IoCs to be disseminated to ... |
|
Check Point R8010 Security Management Architecture Overview
Automation API orchestrates workflows, enabling security alignment with IT processes and systems Page 3 MAIN COMPONENTS OF THE R80 10 SECURITY |
|
Secure Cloud Transformation - Check Point Software
in cloud and security design concepts and generic security architectural concepts This diagram shows the current situation for most enterprises when they start to The SASE model covers a wide range of functionalities, ranging from layer 3 |
|
Word Template - Check Point Software
This behavior reiterates the need to segment the Page 3 ©2018 Check Point Software Technologies Ltd All rights reserved P 3 Check Point Secure Cloud |
|
Word Template - Check Point Software
12 sept 2016 · Topic: Introduction to Check Point Architecture 3-tiered architecture You are presenting an in-house overview of the new features of Check |
|
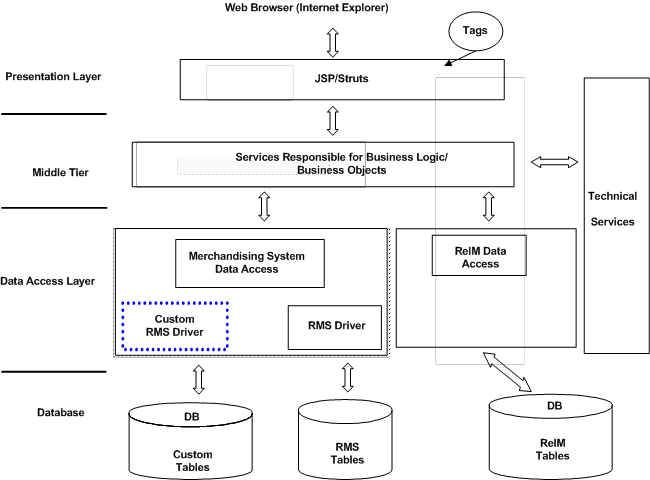
3-Tier Architecture
7 0 Client/Server 2-Tier Architecture 8 0 3-Tier Client/Server Architecture See diagram of N-Tier Architecture for an overview of all these technologies and |
|
Architecting for the Cloud - e-Disciplinas
4 3 3 How to architect for the Cloud - Principles and Considerations 41 Figure 2 4 NIST Cloud Computing Reference Architecture overview [ S72] Figure 4 1 Figure 4 24 Proposed Two-tier SaaS architecture [S43] Figure 4 25 checkpoint system and improving performance and security Study [S54] |
|
ICT Architecture - European Commission - europaeu
Chapter 3: Describes the Application Landscape and preferable options to be used at the Application Checkpoint R75 40 2-nodes clusters; • Cisco ASA; The following picture presents an overview of them Figure 4: server environments or a mixed architecture where some tiers may share one server environment |
|
SmartEvent Datasheet - CheckFirewallscom
21 mar 2018 · 2018 Check Point Software Technologies Ltd All rights reserved [Protected] TOP TIER REPORTING 3 SmartEvent: Full Threat Visibility Datasheet CORRELATION Real-Time Forensic Instead, it's characterized by an architecture that unifies all networks, cloud, and PDF and Excel Integrated |
|
High Availability in Clouds - CORE
presents an overview regarding HA Cloud solutions; “Results description” We understand our 3-layer classification covers the SAF framework its infrastructure, it should configure the checkpoint ser- address and multi-tier architecture) |
|
Architecture du Système Oracle 10g - UV
Chapitre 3 : Structure logique de stockage o Connexion Multi Tiers : Dans une architecture multi tiers, la machine de l'utilisateur se o Lors d'un checkpoint |