secure enclave
|
Apple Platform Security
Secure Enclave Boot ROM The Secure Enclave includes a dedicated Secure Enclave Boot ROM Like the Application Processor Boot ROM the Secure Enclave Boot |
|
Demystifying the Secure Enclave Processor
▫ Fingerprint data cryptographic keys etc Page 4 Secure Enclave Processor • Security circuit designed to perform secure services for the rest of the SOC |
|
Secure Enclaves:
Secure Enclaves are sets of security-related instruction codes built into new CPUs secure enclave Available from every major chip cloud and system vendor |
|
Sécurité des plateformes
Secure Enclave Le Secure Enclave est un système sur une puce (SoC) intégré à toutes les générations récentes d'iPhone d'iPad d'Apple Watch d'Apple TV et |
|
Sécurité des plateformes
La Secure Enclave est la structure sur laquelle reposent le chiffrement des données au repos le démarrage sécurisé dans macOS et les données biométriques |
|
Towards Democratizing Secure Enclave Programming
Abstract— Secure enclaves like Intel SGX provide a means to process data securely on third-party cloud infrastructure with little or no |
|
Unified Enclave Abstraction and Secure Enclave Migration on
Unified enclave abstraction and secure enclave migration on heterogeneous security architectures pdf Dec 2021 [17] Ngabonziza B Martin D Bailey A Cho H |
|
What is the EdgeLock Secure Enclavepdf NXP Community
EDGELOCK SECURE ENCLAVE SECURE CHANNELS Secure Enclave Attestation Data EDGELOCK™ SECURE ENCLAVE SECURE CRYPTO KEY MANAGEMENT Page 26 2 6 PUBLIC |
|
White Paper
The purpose of this design document is to propose an IT security framework that conforms to established design principles and to provide details about solutions |
|
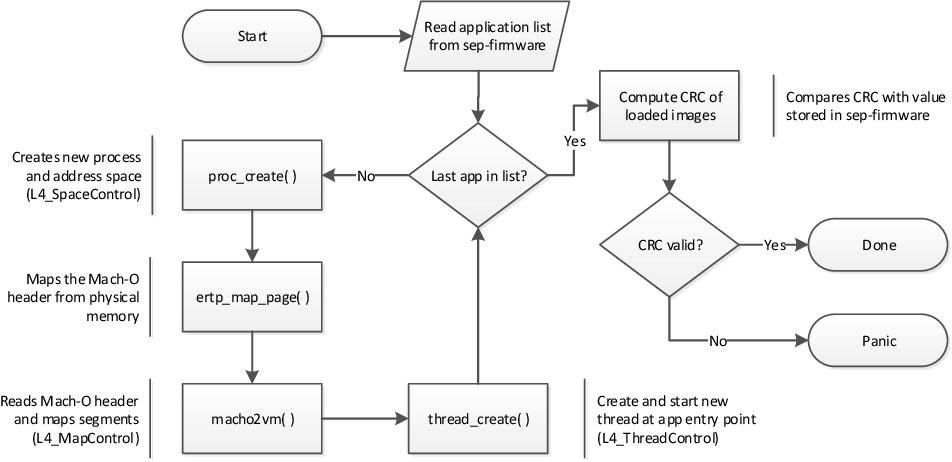
Demystifying the Secure Enclave Processor
Patent US8832465 – Security enclave processor for a system on a chip Part 1: Secure Enclave Processor. ? Hardware Design. ? Boot Process. |
|
Komodo: Using verification to disentangle secure-enclave hardware
2017?10?28? Intel SGX promises powerful security: an arbitrary number of user-mode enclaves protected against physical attacks and privileged software ... |
|
Cisco UCS Secure Enclave Data Center Solution for EMC VSPEX
Cisco Secure Enclaves segments infrastructure into isolated areas that provide access controls visibility |
|
Cisco Secure Enclaves Architecture White Paper
Design guide for Cisco Secure Enclaves Architecture. Figure 5 introduces the Cisco ASA platforms to a secure enclave as a clustered service. |
|
JMD Secure Enclave Privacy Impact Assessment
The tools that are hosted in the Secure Enclave will inherit certain security controls implemented and assessed under this. PIA. 2.2 Indicate the legal |
|
Keystone Enclave An Open-Source Secure Enclave for RISC-V
What is a Secure Enclave? OS. Applications. Trustworthy. Hardware. User. Program and Data. Enclave contents. Integrity Confidentiality. Remote. Attestation |
|
October 2018
Page 3. Introduction. Page 4. Secure Enclave. Page 5. Storage Encryption. APFS encrypted storage. Internal volume encryption and FileVault. |
|
Secure Enclaves for Dummies.pdf
Secure Enclaves For Dummies® Anjuna Security Special Edition. Published by. John Wiley & Sons |
|
Intel SGX: Enclave:
Enclave Based Security: Intel designed Intel® Software Guard Extensions to protect against both hardware and software attacks. For software protection:. |
|
Komodo: Using Verification to Disentangle Secure-Enclave
Prototype on ARM TrustZone. Secure-world memory is isolated from normal world. Komodo Monitor. Untrusted OS. Enclaves. User apps. Privileged modes:. |
|
Apple Platform Security
The Secure Enclave is a dedicated secure subsystem in the latest versions of iPhone iPad iPod touch Mac Apple TV Apple Watch and HomePod Overview |
|
Secure Enclave - Assistance Apple (MA)
17 mai 2021 · The Secure Enclave is isolated from the main processor to provide an extra layer of security and is designed to keep sensitive user data secure |
|
Demystifying the Secure Enclave Processor - Black Hat
Secure Enclave Processor • Security circuit designed to perform secure services for the rest of the SOC ? Prevents main processor from gaining direct |
|
White Paper - Cisco Secure Enclaves Architecture
The purpose of this design document is to propose an IT security framework that conforms to established design principles and to provide details about solutions |
|
Secure enclave - NXP Community
Generate ? Random value that can't easily be guessed • Establish ? Set up keys between corresponding entities • Store |
|
Sécurité des plateformes - Mémoire Vive
La Secure Enclave est la structure sur laquelle reposent le chiffrement des données au repos le démarrage sécurisé dans macOS et les données biométriques |
|
Towards Democratizing Secure Enclave Programming
Secure enclaves like Intel SGX provide a means to process data securely on third-party cloud infrastructure with little or no performance overhead Developing |
|
Intel SGX: Enclave:
The enclave is basically a separated and encrypted region for code and data The enclave is only decrypted inside the processor so it is even safe from the RAM |
|
Keystone Enclave - RISC-V
Keystone Enclave An Open-Source Secure Enclave for RISC-V Dayeol Lee12 David Kohlbrenner Kevin Cheang1 Cameron Rasmussen1 Kevin Laeufer1 Ian Fang |
|
Hardening of cryptographic operations through the use of Secure
14 mai 2021 · Secure enclaves can help solve this problem by creating a secure environment where code can be executed securely guaranteeing that no |
| Cisco Secure Enclaves Architecture White Paper |
| SGX Secure Enclaves in Practice - Black Hat Briefings |
| Towards Democratizing Secure Enclave Programming |
| Searches related to secure enclave filetype:pdf |
How to use enclave in reverse engineering?
- Write enclave program (no secrets) 2.
. Get it attested (signed, bound to a CPU) 3.
. Provision secrets, from a remote client 4.
. Run enclave program in the CPU 5.
. Get the result, and a proof that it's the result of the intended computation Example: make reverse engineer impossible 1.
. Enclave generates a key pair a.
. Seals the private key b.
What is required to develop SGX enclaves?
- Required to develop SGX enclaves and applications under Visual Studio 2012 Professional (not free, license needed). ? SGX libs: Intel-custom libc and crypto lib, each coming in two versions, debug and release ? Tools: ? sgx_edger8r to generate glue code ? sgx_sign to sign enclaves with our dev key ? Example code, not fully reliable
Is there an AES-NI implementation for enclaves?
- No AES-NI, textbook implementation instead (slower) S-box = 256-byte table with basic cache-timing mitigation However, AES in prebuilt enclaves to use AES-NI
|
Dedicated Security Chips in the Age of Secure Enclaves
Secure enclave architectures have become prevalent in modern CPUs and enclaves provide a flexible way to im- plement various hardware-assisted security |
|
Keystone Enclave An Open-Source Secure Enclave for RISC-V
What is a Secure Enclave? OS Applications Trustworthy Hardware User Program and Data Enclave contents Integrity Confidentiality Remote Attestation |
|
Cisco Secure Enclaves Architecture White Paper
2014 Cisco and/or its affiliates All rights reserved This document is Cisco Public Page 1 of 23 White Paper Cisco Secure Enclaves Architecture Design Guide |
|
Sécurité des plateformes - Apple
Secure Enclave équipant les appareils iOS, iPadOS, watchOS et tvOS récents ainsi que tous les ordinateurs dotés de la puce Apple T2 Security La Secure |
|
Apple T2 Security Chip Security Overview
These capabilities combine to provide unrivaled privacy and security features never before present on Mac The Secure Enclave is a coprocessor fabricated |
|
Secure Enclaves: - Anjuna Security
A secure enclave provides CPU hardware-level isolation and memory encryption on every server, by isolating application code and data from anyone with |
|
IOS Security Guide - DermNet NZ
Secure boot chain System Software Authorization Secure Enclave Touch ID Page 10 Encryption and Data Protection Hardware security features File Data |


![Demystifying Secure enclave processor - [PDF Document] Demystifying Secure enclave processor - [PDF Document]](https://www.anjuna.io/hubfs/Icons%20And%20Graphics/Secure%20Enclaves%20Prevent%20Critical%20Threats.png)







![Demystifying Secure enclave processor - [PDF Document] Demystifying Secure enclave processor - [PDF Document]](https://d3i71xaburhd42.cloudfront.net/c49e4392041d15e26319e048aeefa2e09e181416/34-Figure7-1.png)
