apple report phishing
How do I report phishing attempts?
There are a number of resources that you can use to report phishing attempts, both to companies and to the government. Company's like Apple and Facebook often have email addresses specifically for forwarding phishing attempts, while Google has a button in Gmail that lets you do just that.
How do I forward phishing emails?
Company's like Apple and Facebook often have email addresses specifically for forwarding phishing attempts, while Google has a button in Gmail that lets you do just that. When using the following links, be sure to forward the phishing email that you're reporting:
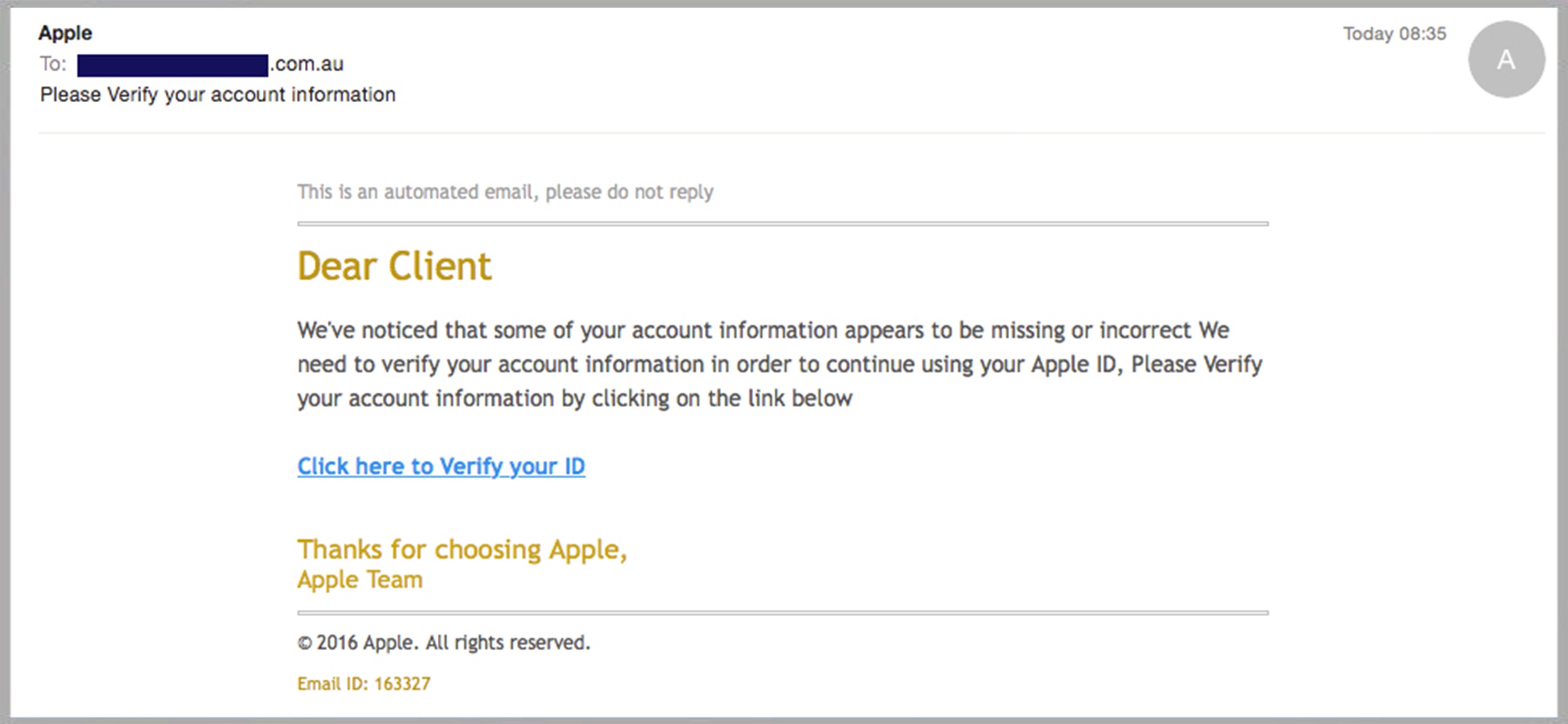
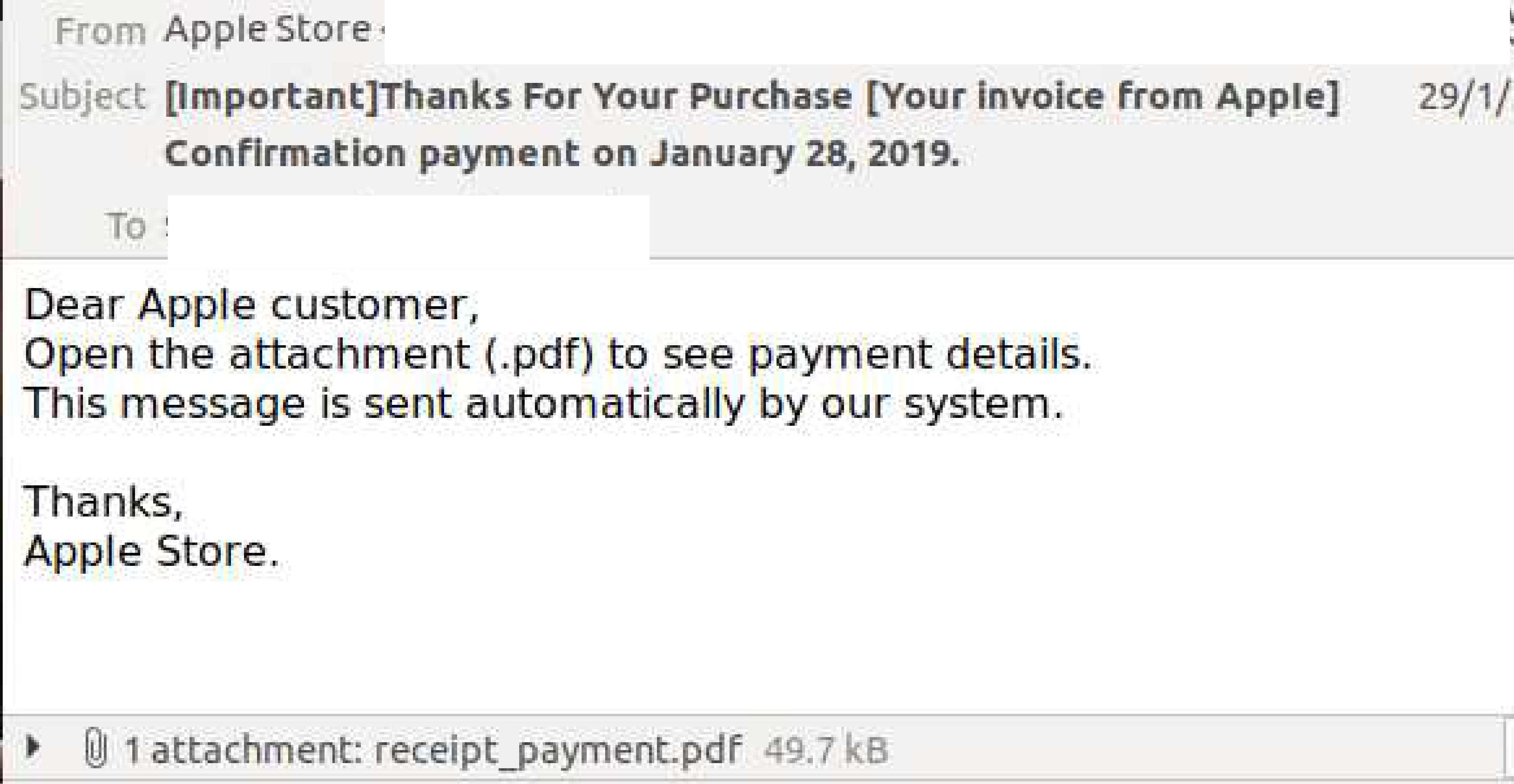
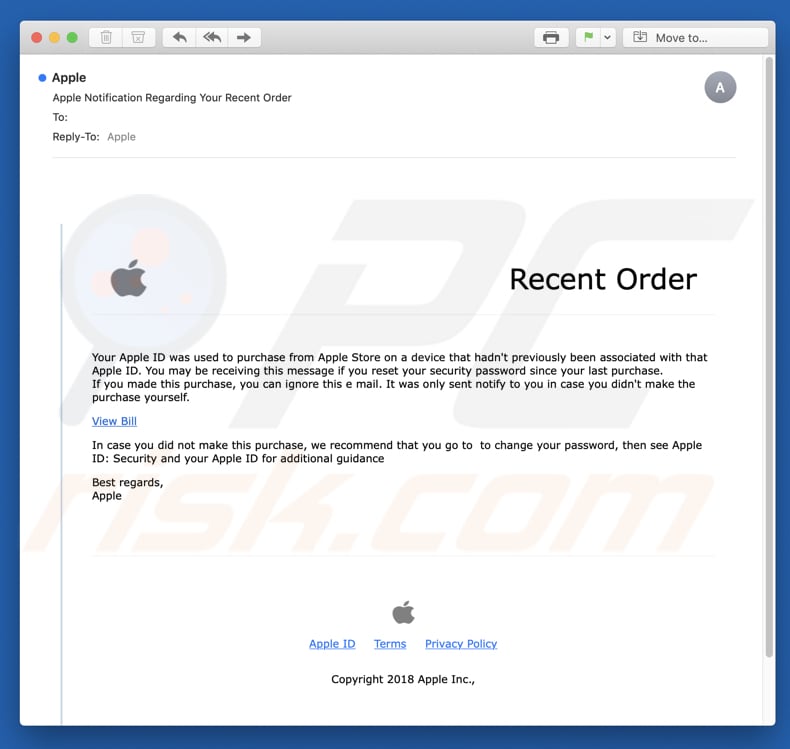
What if I receive a suspicious email from Apple?
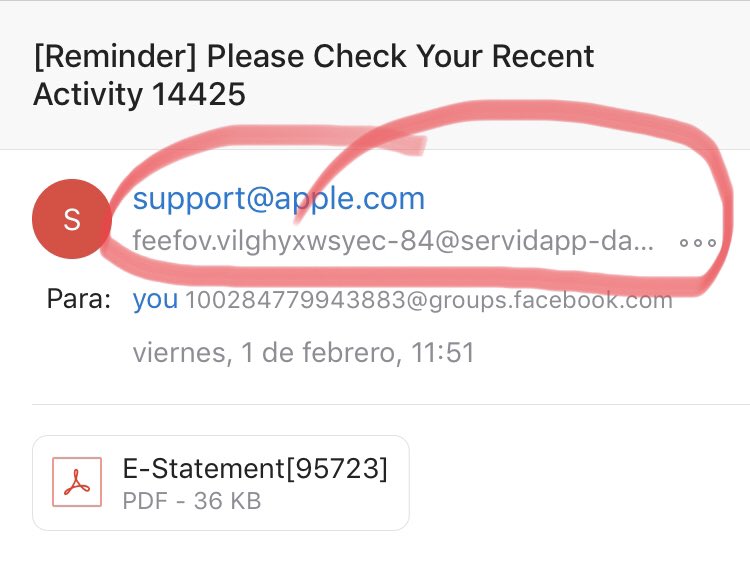
If you receive a suspicious email that's designed to look like it’s from Apple, you can forward it to reportphishing@apple.com. Learn more about phishing and other scams. If you lose your device or think it might be stolen, these articles might help you find it and protect your information.
What is a phishing scam?
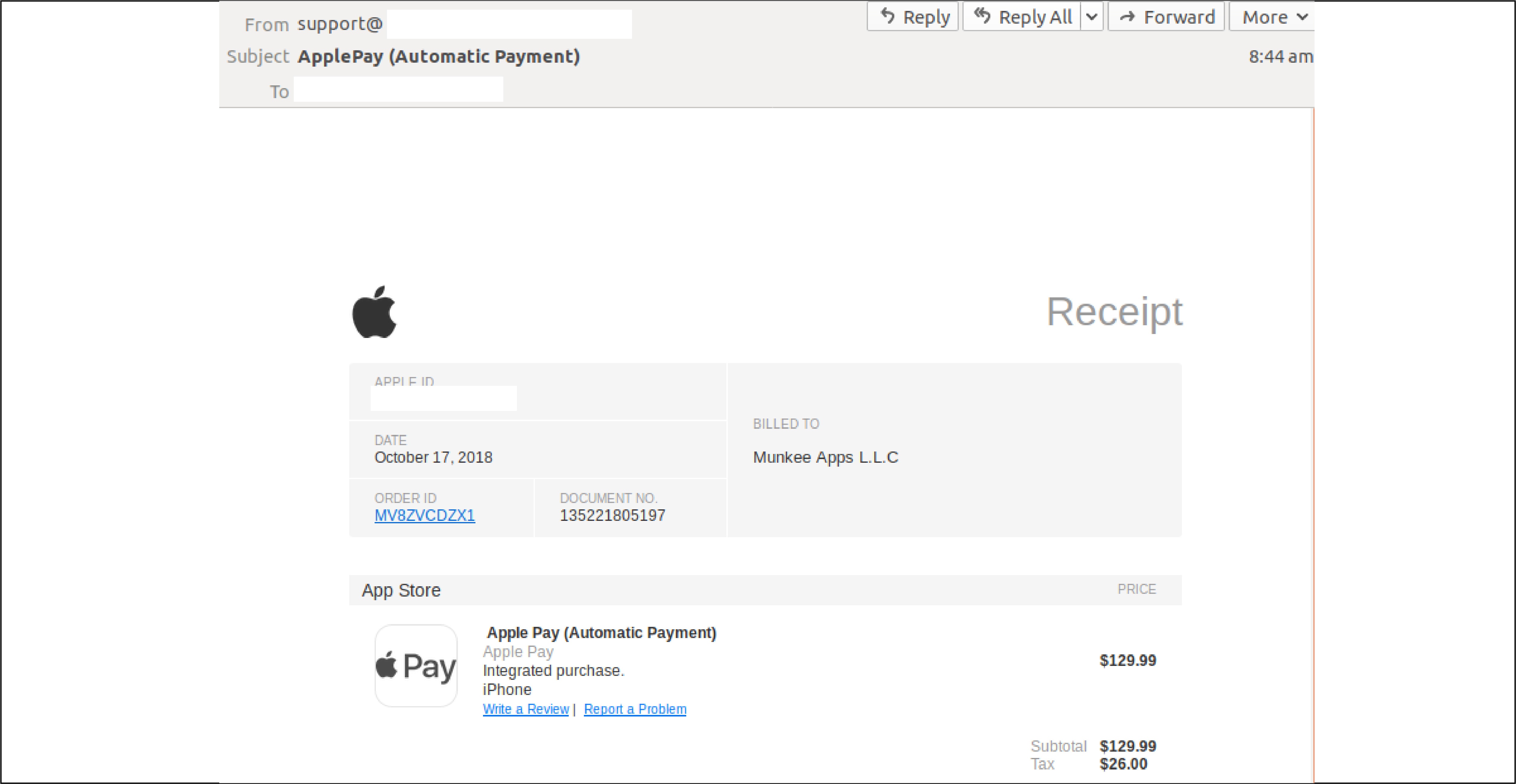
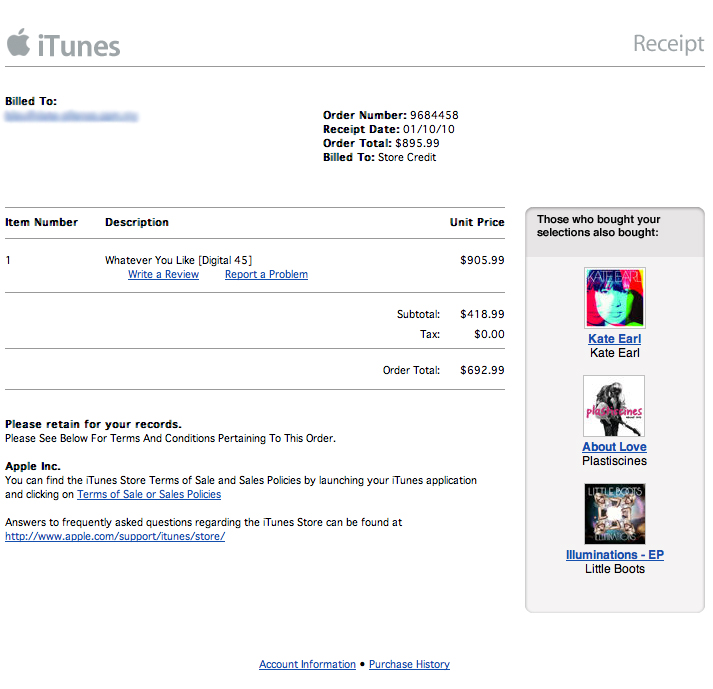
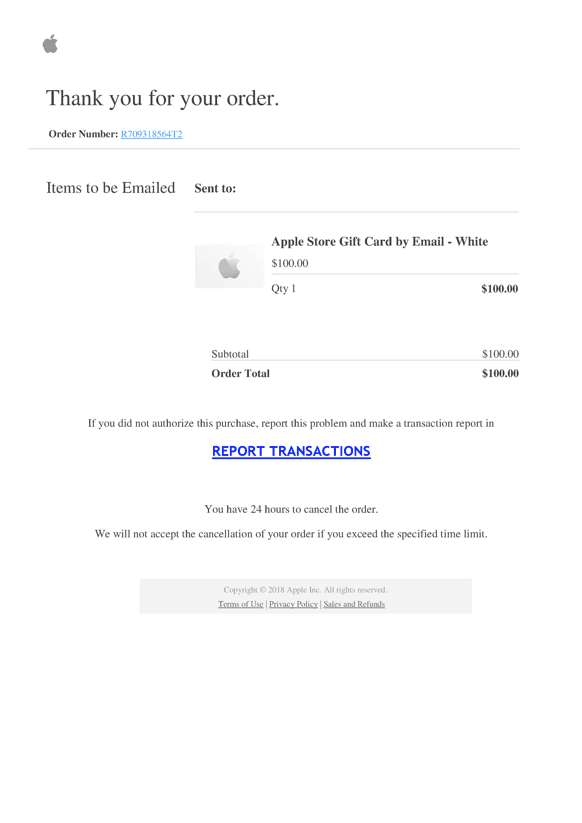
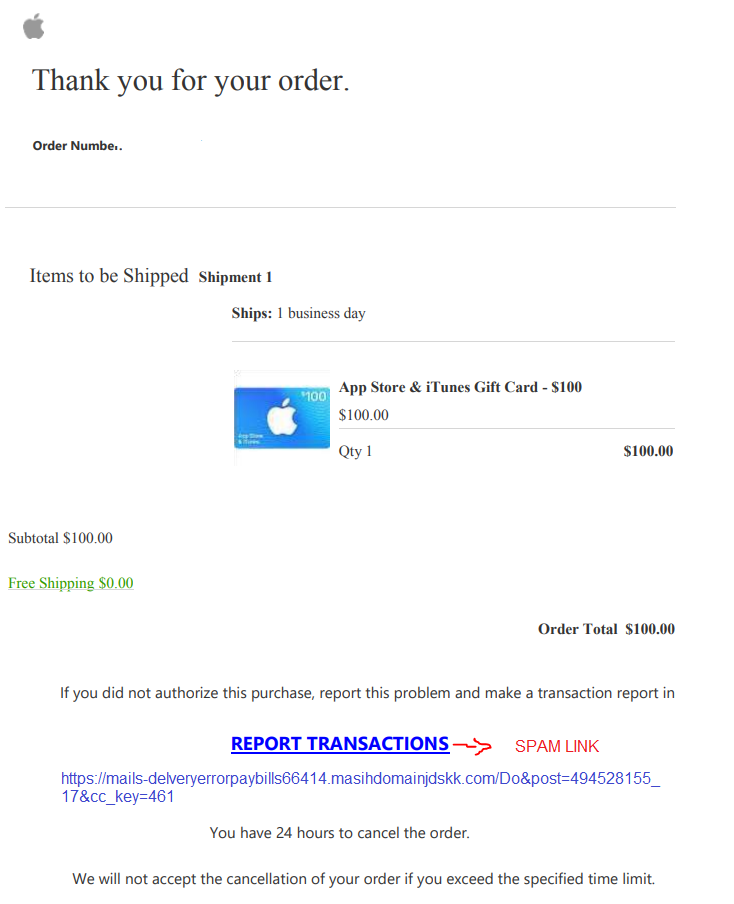
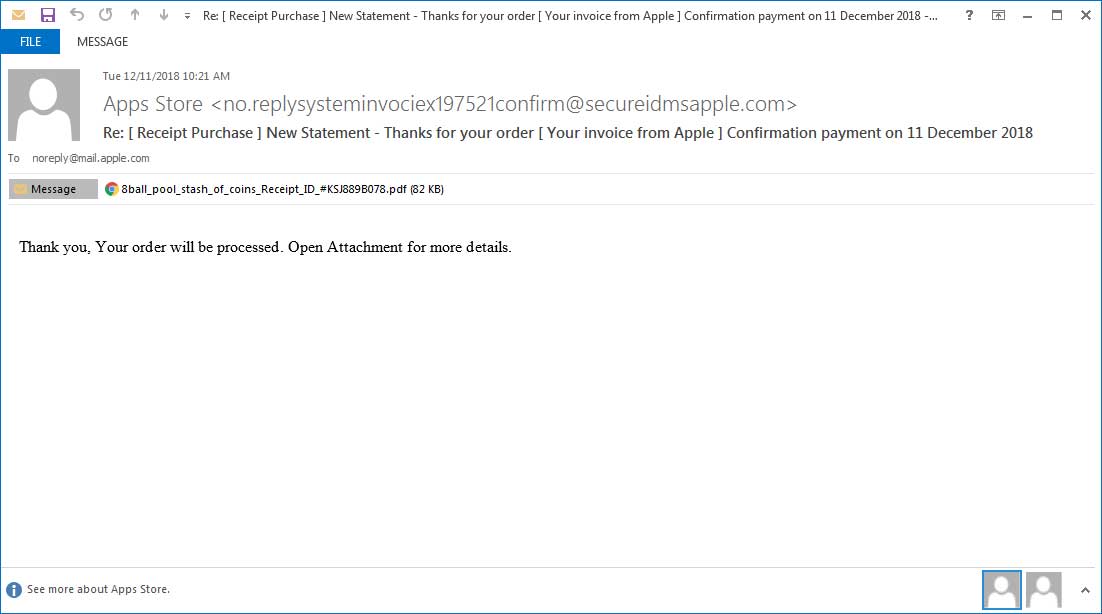
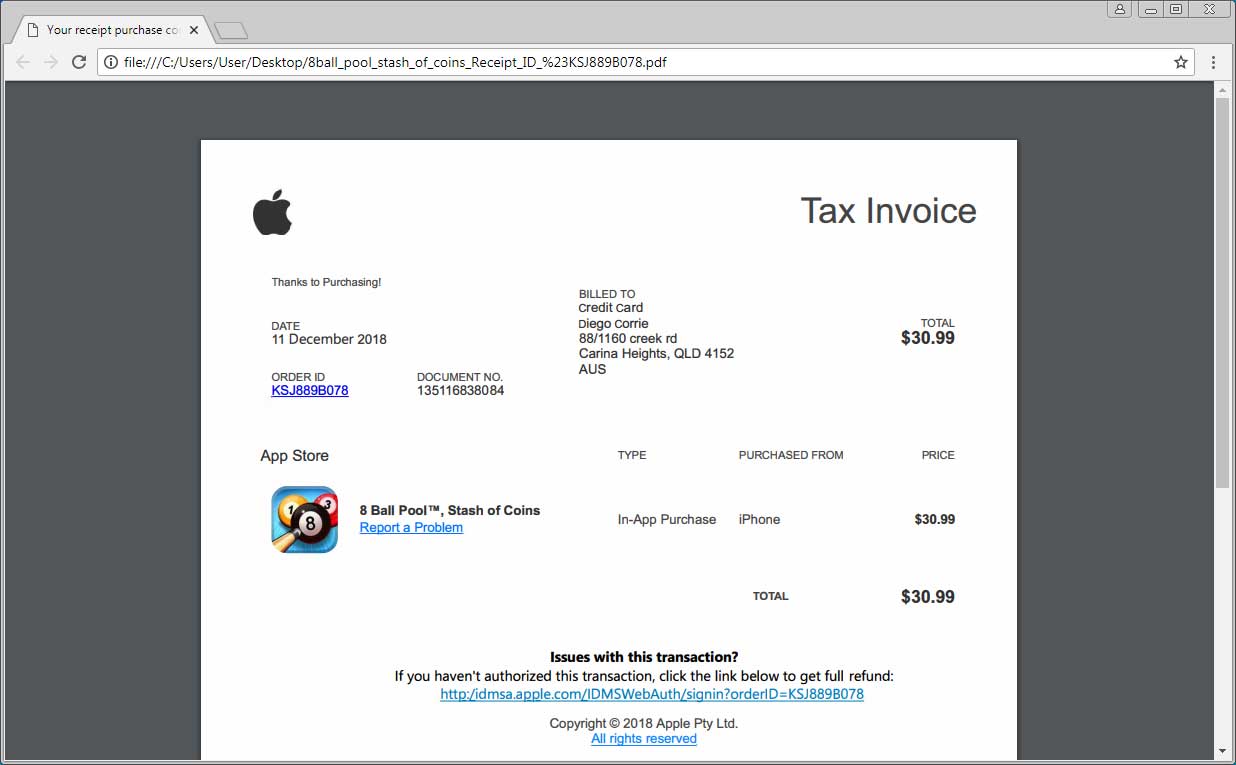
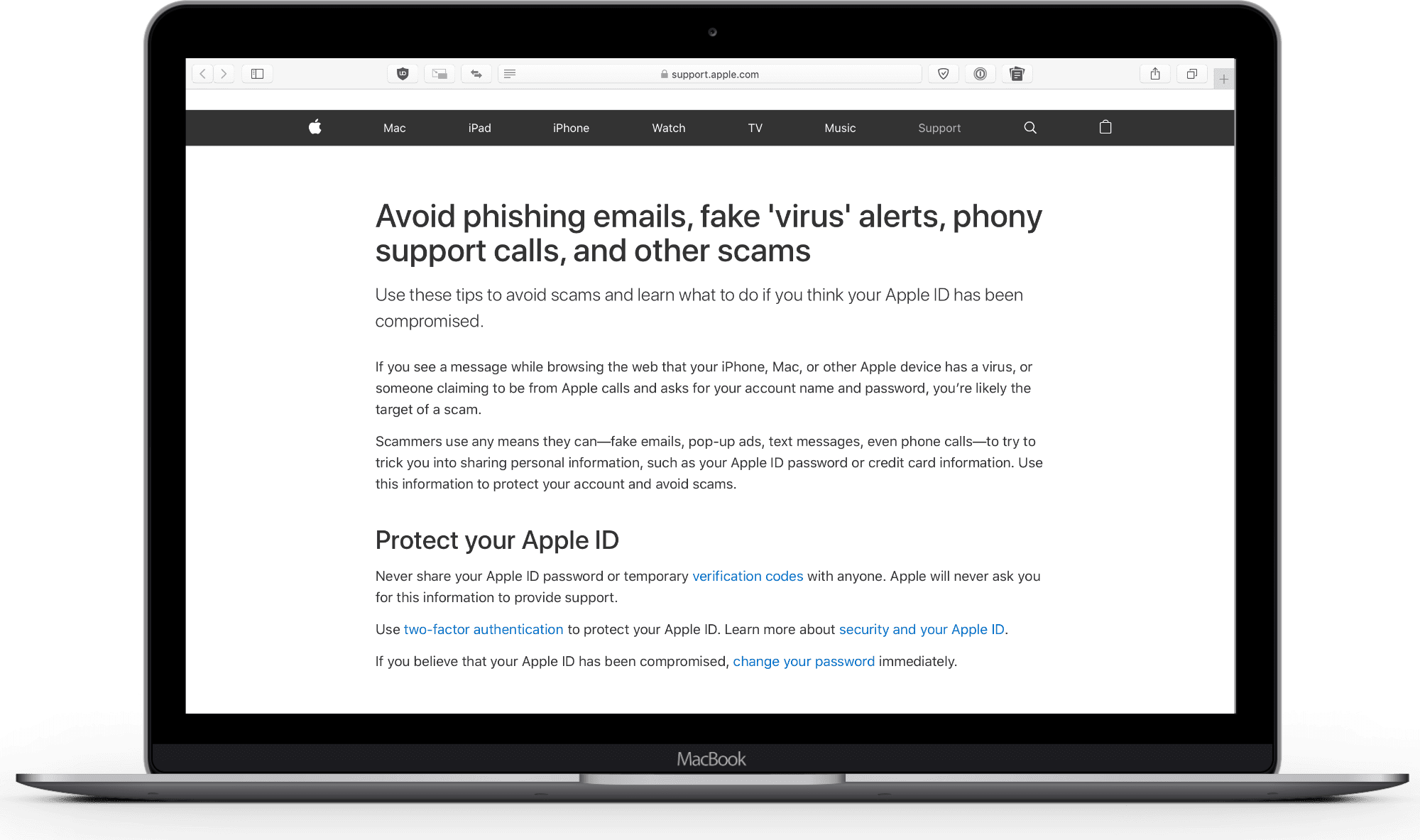
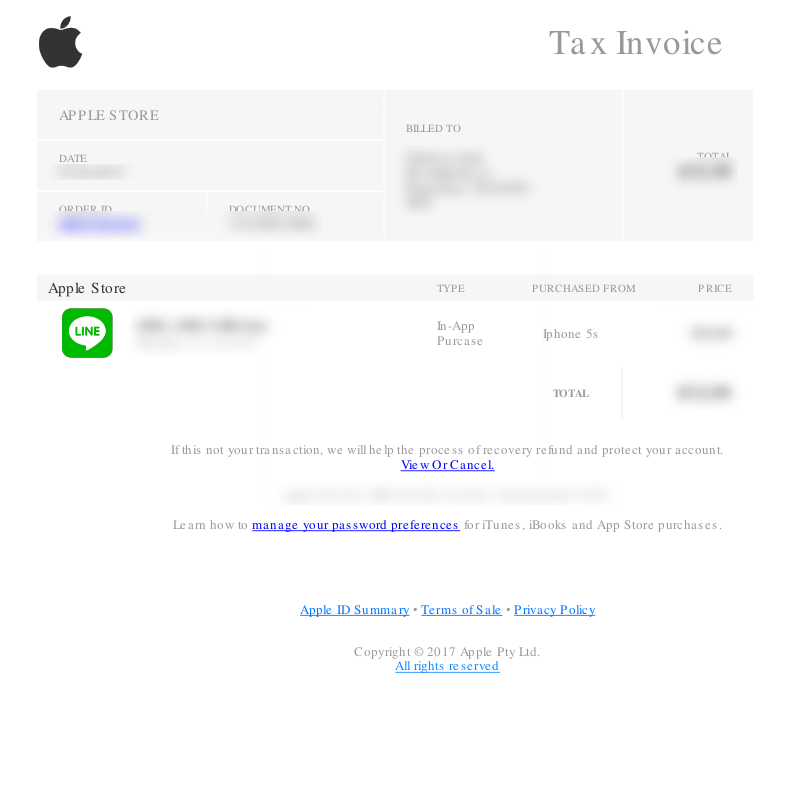
Scammers use phishing and other types of social engineering to try to trick you into sharing personal information—such as your Apple ID password or credit card information. It can happen by email, phone, text message, or even through pop-up notifications when you’re browsing the web.

How to identify avoid and report phishing — Apple Support

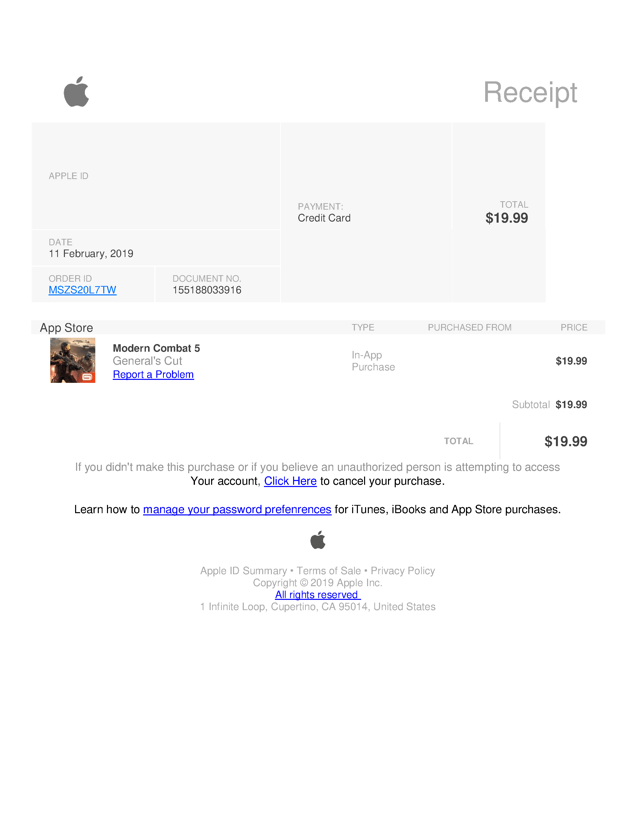
How to Identify Apple ID Phishing Attempts

Apple ID Phishing Email Scam
|
Apple Transparency Report: Government and Private Party Requests
30 juin 2020 In credit card fraud cases law enforcement generally seek details of suspected fraudulent transactions. Depending on what the legal request ... |
|
Apple Transparency Report: Government and Private Party Requests
31 déc. 2020 In credit card fraud cases law enforcement generally seek details of suspected fraudulent transactions. Depending on what the legal request ... |
|
Building a Trusted Ecosystem for Millions of Apps - A threat analysis
In the rare cases in which a fraudulent or malicious app makes it onto the App Store Apple can remove it once discovered and block any of its future |
|
Report on Government and Private Party Requests for Customer
30 juin 2018 report provides information regarding requests Apple received from ... credit card fraud cases law enforcement generally seek details of ... |
|
Apple Transparency Report: Government and Private Party Requests
30 juin 2019 credit card fraud cases law enforcement generally seek details of suspected fraudulent transactions. Depending on what the legal request ... |
|
Report on Government and Private Party Requests for Customer
31 déc. 2017 details of customers associated with devices or device connections to Apple services. In credit card fraud cases law enforcement generally ... |
|
Apple Transparency Report: Government and Private Party Requests
31 déc. 2019 In credit card fraud cases law enforcement generally seek details of suspected fraudulent transactions. Depending on what the legal request ... |
|
Apple Transparency Report: Government and Private Party Requests
30 juin 2021 In credit card fraud cases law enforcement generally seek details of suspected fraudulent transactions. Depending on what the legal request ... |
|
Apple Transparency Report: Government and Private Party Requests
31 déc. 2018 In credit card fraud cases law enforcement generally seek details of suspected fraudulent transactions. Depending on what the legal request ... |
|
Apple-platform-security-guide.pdf
To learn more about reporting issues to Apple and subscribing to security that even software running with root privileges or in the kernel can't spoof. |
|
Apple id fake email report - Squarespace
Use these tips to avoid scams and learn what to do if you think your Apple ID has been compromised Phishing refers to fraudulent attempts to obtain personal |
|
Apple Transparency Report: Government and Private Party Requests
31 déc 2018 · credit card fraud cases, law enforcement generally seek details of suspected fraudulent transactions Depending on what the legal request asks |
|
Apple support email address to report phishing - Simple Storage
If you don't have Report as Phishing, click here If you believe you've encountered a phish or clicked url in a suspicious email, etc We hope you enjoy the article, |
|
[Apple ID/iCloud Phishing Scam] NHWA alert Fraudsters are
Fraudsters are sending phishing texts and e-mail messages to members of the you believe to be a phishing message purporting to be from Apple, report it to |
|
Recognizing Online Scams - Intel
If you use e-mail, you are likely to run into a phishing scam at some point Common characteristics of phishing e-mails include: From the Apple menu: |
|
Healthcare Phishing - Office of the Director of National Intelligence
Appendix B: Where to Report Phishing 8 See, e g , Jindrich Karasek, New Phishing Scam Uses AES Encryption and Goes After Apple IDs, available at |
|
Phishing Dont be fooled - Homeland Security
Appendix B: Where to Report Phishing 8 See, e g , Jindrich Karasek, New Phishing Scam Uses AES Encryption and Goes After Apple IDs, available at |











![Fw: [ REMINDER ] - Review recent login attempts on your Apple ID Fw: [ REMINDER ] - Review recent login attempts on your Apple ID](https://www.itgovernance.co.uk/blog/wp-content/uploads/2019/09/Appleid-phishing.png)