citrix security
l'application Citrix Workspace pour Windows).
Cliquez avec le bouton droit sur le fichier d'exécution Citrix Workspace App, puis sélectionnez Run as administrator (Exécuter en tant qu'administrateur).
Cliquez sur Start (Démarrer) dans l'écran de bienvenue.
|
Best Practices for Enterprise Security Citrix
Best Practices for Enterprise Security • Citrix XenApp and XenDesktop to manage apps and desktops centrally inside the data center |
|
Putting the “Security” in Secure Remote Access Citrix ADC
Citrix ADC is not only a leading Application Delivery Controller (ADC) but also a secure remote access solution that provides security and |
|
10 reasons to strengthen security with app and desktop virtualization
The core of the solution is Citrix XenApp® for app virtualization and Citrix XenDesktop® which integrates the full power of XenApp for Page 5 White Paper |
|
Garantir la sécurité effective de laccès distant sécurisé - Citrix
Ce livre blanc décrit l'une des principales forces qui fait de Citrix NetScaler Unified Gateway la solution idéale en matière de sécurité des applications à |
|
Citrix Security Development Lifecycle
Citrix has a dedicated Security Engineering organization responsible for the security of all Citrix products and services The organization works closely with |
|
Secure remote access to any application from anywhere on - Citrix
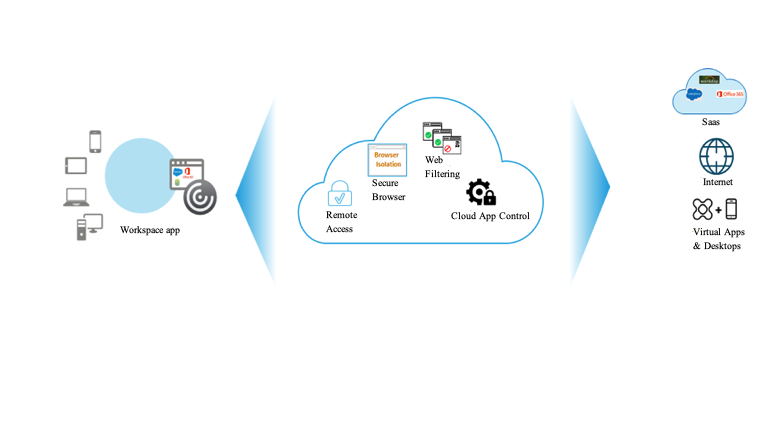
Citrix Secure Workspace Access offers a comprehensive zero trust approach that delivers secure and contextual access to all applications you need and provides |
|
Overcoming BYOD security risks Citrix
Overcoming BYOD security risks How organisations can take advantage of Citrix technology to provide a secure platform for remote working |
|
CITRIX SUPPLIER SECURITY STANDARDS
security compliance requirements may be specified in Supplier's Agreement or individual statement of work The Standards contain the following sections: |
|
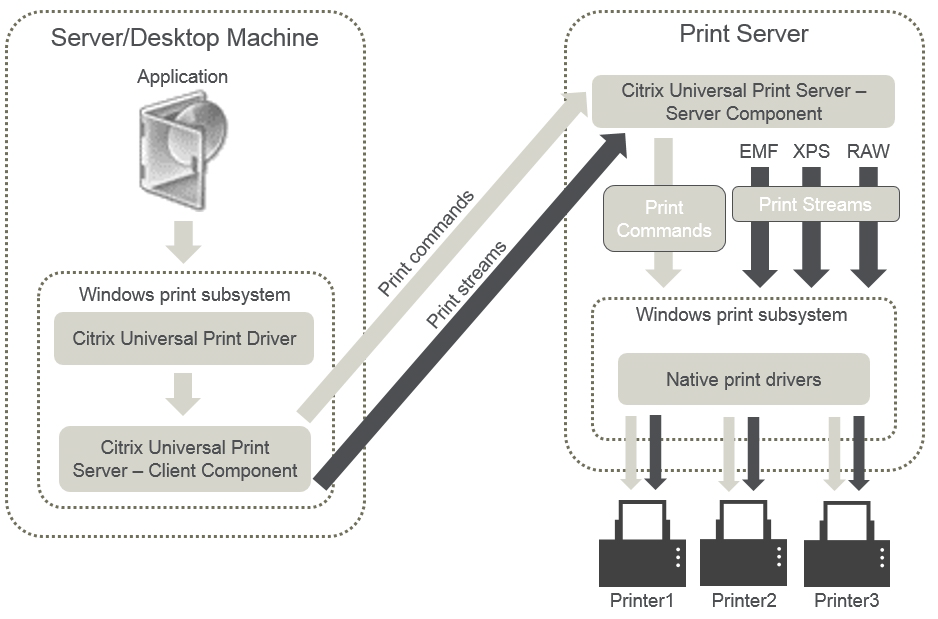
Secure app and data delivery - across devices networks and - Citrix
devices networks and locations How Citrix Virtual Apps dramatically simplifies data protection access control and other critical security tasks |
|
La sécurité mise à disposition dans le cloud pour le Digital Workspace
Citrix Secure Access Service Edge Citrix Secure Internet Access (SIA) propose des Security Broker la prévention contre les pertes de |
|
Best practices for enterprise security - Citrix
Citrix supports best practices for risk management across five key pillars of enterprise security: identity and access, network security, application security, data |
|
Garantir la sécurité effective de laccès distant sécurisé - Citrix
Ce livre blanc décrit l'une des principales forces qui fait de Citrix NetScaler Unified Gateway la solution idéale en matière de sécurité des applications à distance, |
|
Putting the Security in Secure Remote Access - Citrix
Citrix ADC is not only a leading Application Delivery Controller (ADC), but also a secure remote access solution that provides security and compliance beyond |
|
10 reasons to strengthen security with app and desktop - Citrix
At the same time, desktop virtualization, complemented by secure file sharing and enterprise mobility management, helps fortify information security and |
|
Secure remote access to any application from anywhere, on - Citrix
At Citrix, we empower our customers to provide contextual and secure access to applications deployed on-premises, in the cloud, or delivered as SaaS In |
|
Secure app and data delivery - across devices, networks, and - Citrix
delivery - across devices, networks, and locations How Citrix Virtual Apps dramatically simplifies data protection, access control, and other critical security tasks |
|
Citrix XenMobile Service Security
Citrix has been helping the largest companies in the world secure their apps and data for nearly three decades Security is a fundamental part of all Citrix |
|
Annexe sur la sécurité des Services Citrix
contrôles de sécurité mis en place dans le cadre des Citrix Cloud Services, des Citrix applique un programme de gestion des risques de sécurité (Security |
|
Citrix Cloud Solution for Compliance
requirements deal with data and process security and control A centralized A secure bridge and access between cloud and enterprise data center A secure |
|
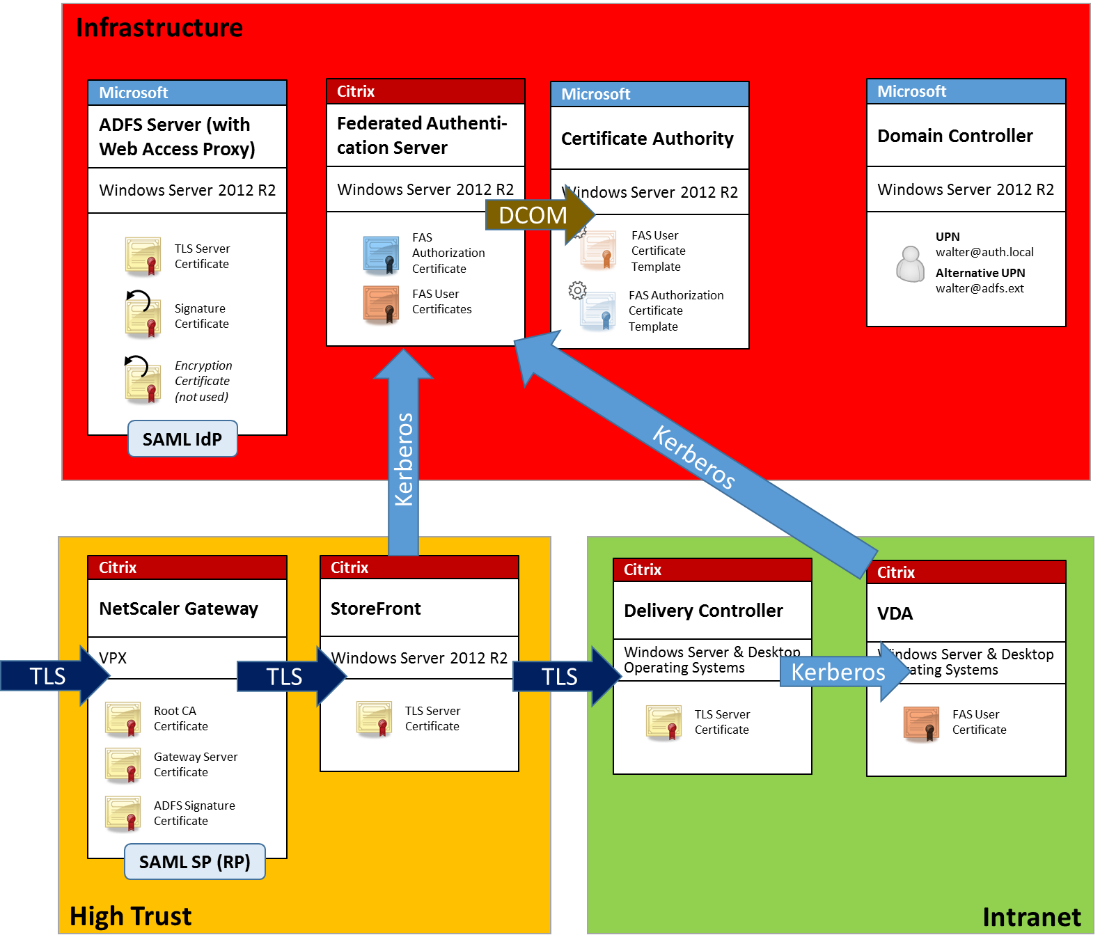
End-To-End Encryption with XenApp and XenDesktop
configuring the Transport Layer Security (TLS) protocol This white paper builds on the guidance in the white paper “Getting Started with Citrix XenApp |




![1Y0-340 PDF [2020] - Real Citrix 1Y0-340 Exam PDF Pages 1 - 8 1Y0-340 PDF [2020] - Real Citrix 1Y0-340 Exam PDF Pages 1 - 8](https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/media/hdx-1.png)