information security program plan example
|
Michigan Technological University Information Security Plan
Security and Information Compliance Officers are responsible for the University's security programs including risk management. They play a leading role in |
|
Information Security Program Plan
11 Nov 2015 Areas that fall under the scope of industry regulatory |
|
Creating a Written Information Security Plan for your Tax
As a part of the plan the FTC requires each firm to: • Designate one or more employees to coordinate its information security program. • Identify and assess |
|
Security-plan-example.pdf
information and procedures associated with this Security Plan. The CIP Cyber Security Awareness Program serves as the first layer of cyber security education. |
|
Final Memorandum - Review of NASAs Information Security Program
14 Apr 2016 Examples of management controls include an ... security program plan to identify requirements for the information security program. |
|
Information Security Plan
Design and Implementation of Safeguards Program Servers must use encrypted protocols instead of their non-encrypted counterparts (example: HTTPS instead of ... |
|
Sample Written Information Security Plan
Sample Written Information Security Plan. I. OBJECTIVE: Our objective in the 3) Use software program that requires each employee to enter a unique log-in ... |
|
Computer Security Incident Handling Guide
The incident response program structure should also be discussed within the plan for example minimizing turnover and burnout and providing a solid training ... |
|
Key Components of an Information Security Metrics Program Plan
literature provides industry best practices and examples of information security metrics currently. Page 18. Key Components of IT Security Metrics Program 14. |
|
Federal Government Cybersecurity Incident and Vulnerability
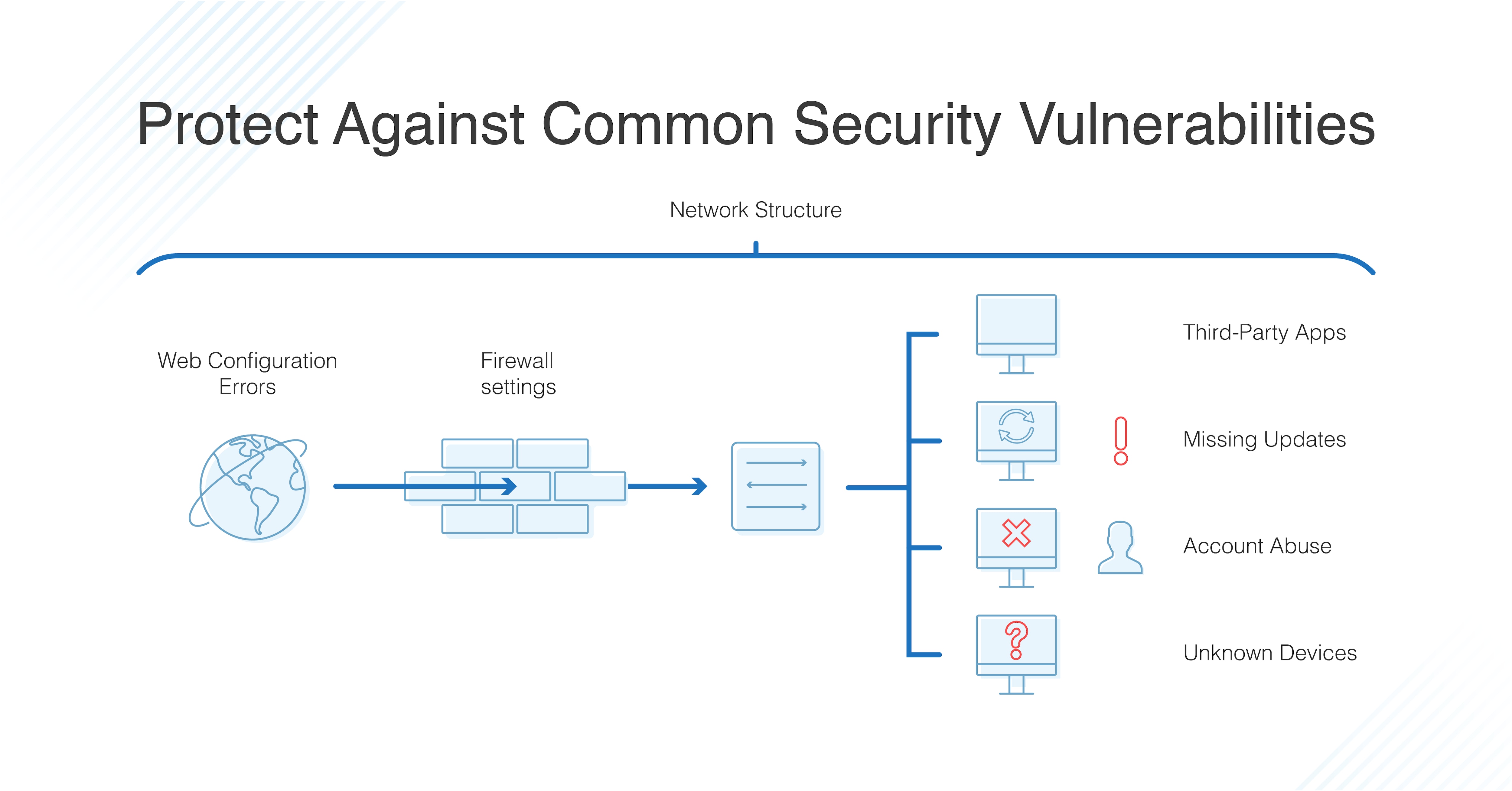
Standard vulnerability management programs include phases for identifying analyzing |
|
Information Security Plan
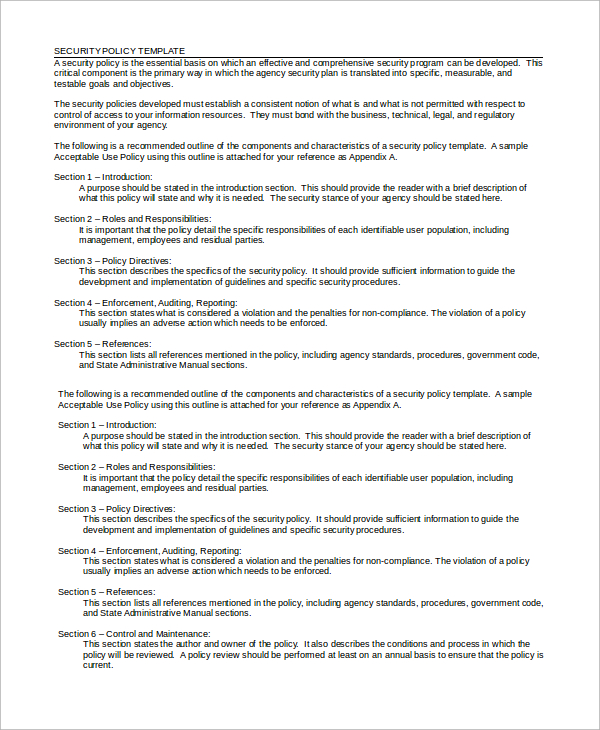
Note to agencies – This security plan template was created to align with the ISO and program source code will be controlled and information technology ... |
|
Information Security Program Plan
11 Nov 2015 Areas that fall under the scope of industry regulatory |
|
Michigan Technological University Information Security Plan
Security and Information Compliance Officers are responsible for the University's security programs including risk management. They play a leading role in |
|
Program Management Policy and Procedures (PM-1)
28 Jan 2022 Establishes and reviews annually the information security strategy. (i.e. program plan) for the Executive Branch of the State of Maine. 8.2.3.2 ... |
|
Sample Information Security Program
The objectives of this Information Security Program (“Program”) are as follows: •. Insure the security and confidentiality of the Dealership's customer |
|
Creating a Written Information Security Plan for your Tax
2 Agu 2022 This document is intended to provide sample information and to help tax professionals particularly smaller practices |
|
Security-plan-example.pdf
with NERC Standard CIP-006-2 Physical Security Program for the Protection of Critical. Cyber Assets. Maintenance and testing (R8) is described in this plan |
|
Army Information Security Program
22 Okt 2019 DA personnel and DA contractors will mark all classified information and material regardless of media (for example |
|
Final Memorandum - Review of NASAs Information Security Program
14 Apr 2016 Examples of management controls include an organization's information security program plan Senior Security Officer |
|
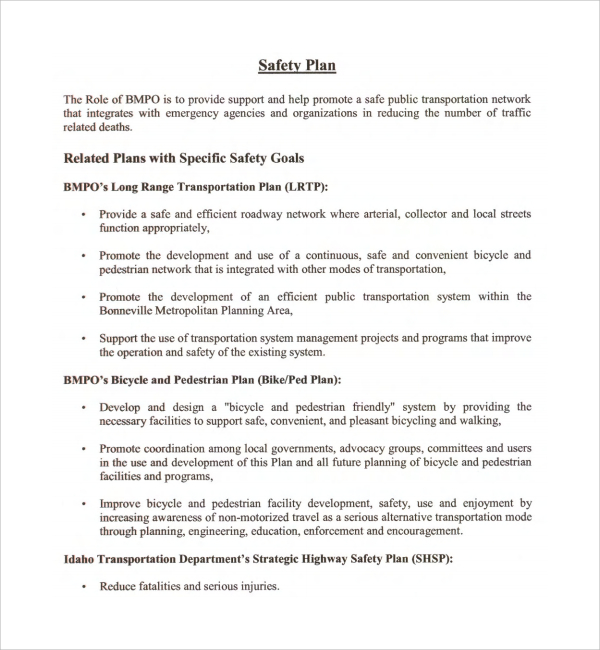
Statewide Information Security Plan
6.1.5 Information Security in project management . The State of Oregon Information Security Plan reflects the continuous improvement of security ... |
|
Information Security Plan - Oregongov
Security Program Information security is a business issue The objective is to identify assess and take steps to avoid or mitigate risk to agency information assets Governance is an essential component for the long-term strategy and direction of an organization with respect to the security policies and risk management |
|
Information Security Plan - Michigan Technological University
Nov 11 2015 · Information Security Objectives: 1 Confidentiality: Preserving authorized restrictions of information access including means for protecting personal privacy and propriety information 2 Integrity: Guarding against improper modification or destruction and includes ensuring information non-repudiation and authenticity 3 |
|
Information Security Plan - Michigan Technological University
An Information Security Plan (ISP) is designed to protect information and critical resources from a wide range of threats in order to ensure business continuity minimize business risk and maximize return on investments and business opportunities Information Technology (IT) security is achieved by implementing a suitable set of |
|
NIST Cybersecurity Framework Policy Template Guide
Information Security Policy ID AM-6 Cybersecurity roles and responsibilities for the entire workforces and third-party stakeholders (e g suppliers customers partners) are established Acceptable Use of Information Technology Resource Policy Information Security Policy Security Awareness and Training Policy Identify: Risk Management Strategy |
|
INFORMATION SECURITY PLAN - kilgoreedu
An InformationSecurity Plan provides direction for managing and protecting the confidentiality integrity and availability of information resources particularly highly sensitive or critical data The plan contains administrative technical and physical safeguards to protect information assets |
|
Searches related to information security program plan example filetype:pdf
A security plan should be appropriate to the company’s size scope of activities complexity and the sensitivity of the customer data it handles There is no one-size-fits-all WISP For example a sole practitioner can use a more abbreviated and simplified plan than a 10-partner accounting firm A good WISP should focus on three areas: |
|
Information Security Plan - Oregongov
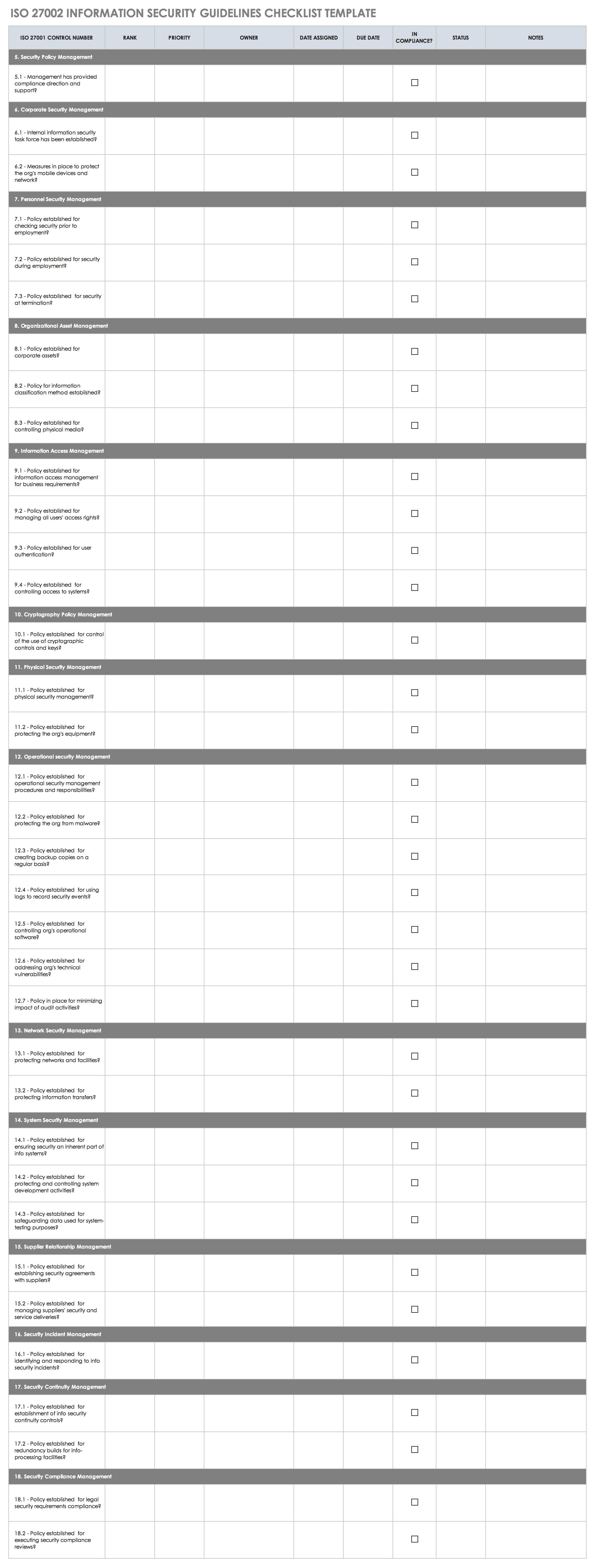
Note to agencies – This security plan template was created to align with the ISO 27002:2005 standard and to meet the requirements of the statewide Information |
|
Michigan Technological University Information Security Plan
The Information Security Plan establishes and states the policies governing Michigan Technological University's IT standards and practices |
|
Information Security Program Plan
11 nov 2015 · This plan details the information security risks facing the UTK Campus as well as the disposition of mitigating or compensating controls |
|
INFORMATION SECURITY PROGRAM (ISP) Strake Cyber
INFORMATION SECURITY PROGRAM STRUCTURE 18 MANAGEMENT DIRECTION FOR INFORMATION SECURITY 18 POLICIES STANDARDS PROCEDURES GUIDELINES STRUCTURE |
|
Sample Written Information Security Plan - State Bar of Wisconsin
Appendix B Sample Written Information Security Plan I OBJECTIVE: Our objective in the development and implementation of this written information |
|
INFORMATION SECURITY PLAN - Kilgore College
An Information Security Plan provides direction for managing and Establish an ongoing security awareness education program for all users starting with |
|
Sample Information Security Program
The Program Coordinator shall conduct a risk assessment to identify reasonably foreseeable internal and external risks to the security confidentiality and |
|
Information Security Stragegic Plan - Minnesotagov
With more advanced and persistent threats large organizations typically run sophisticated tools to help manage cyber risks in real time An example of one such |
|
Information Security Program Plan (ISPP) CIO-IT Security-18-90 - GSA
16 jui 2020 · For example an organization may choose to implement the Incident Response Policy and Procedures security control (IR- 1) as a hybrid control |
What is an information security plan?
- Information Security Plan Page 4 Rev: 3 – 10/13/2011 1 EXECUTIVE SUMMARY An Information Security Plan (ISP) is designed to protect information and critical resources from a wide range of threats in order to ensure business continuity, minimize business risk, and maximize return on investments and business opportunities.
What are the objectives of information security?
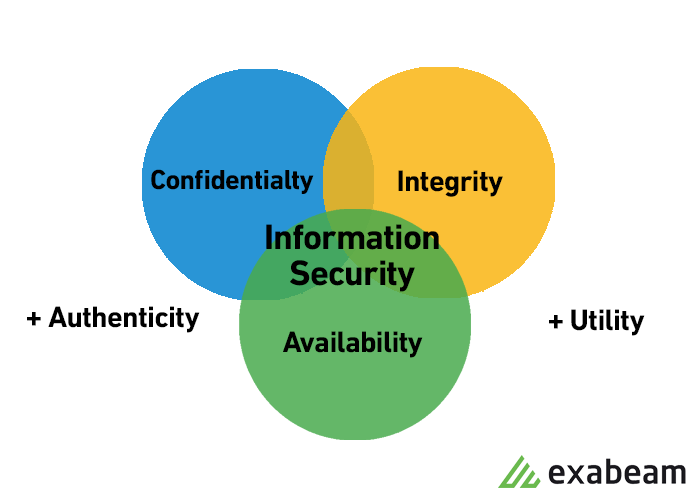
- Information Security Objectives: 1. Confidentiality: Preserving authorized restrictions of information access, including means for protecting personal privacy and propriety information. 2. Integrity: Guarding against improper modification or destruction and includes ensuring information non-repudiation and authenticity.
What are information security policies and procedures?
- Information security policies and procedures represent the foundation for the University’s ISP. Information security policies serve as overarching guidelines for the use, management, and implementation of information security throughout Michigan Tech.
What is Michigan Technological University's information security plan?
- The Information Security Plan establishes and states the policies governing Michigan Technological University’s IT standards and practices. These policies define the University’s objectives for managing operations and lingcontrol activities.
|
Information Security Plan - State of Oregon
Note to agencies – This security plan template was created to align with the ISO and to meet the requirements of the statewide Information Security policy |
|
Sample Information Security Program
The Program Coordinator shall conduct a risk assessment to identify reasonably foreseeable internal and external risks to the security, confidentiality and integrity |
|
Sample Written Information Security Plan - State Bar of Wisconsin
2) Incorporation of privacy policy guidelines into employee handbook 3) Employment agreements amended to require compliance with privacy policy and to |
|
IT Security Plan - University of South Florida
The USF IT Security Plan defines the information security standards and downtime, keep system software programs up-to-date, and prevent problems and gives examples of what is considered misuse of resources and the actions that can |
|
Information Security Program Plan - Office of Information Technology
11 nov 2015 · Areas that fall under the scope of industry, regulatory, or legal requirements, for example, often require additional controls The most common of |
|
Security Plan Example - Federal Energy Regulatory Commission
(Utility)'s security program, and in some sections, makes reference to other relevant plans and information and procedures associated with this Security Plan |
|
Sample Detailed Security Policy - Bowie State University
In this regard, Enterprise IT Security Department conducts an annual risk analysis and remediation report While information systems contingency planning is the |
|
Information Security Program Plan CIO-IT Security-18-90 - GSAgov
Organizations may choose, for example, to implement the Contingency GSA's enterprise-wide Information Security Program Plan, Revision 2, is approved for |
|
The Basic Components of an Information Security Program
tion Security Program, by the Information Security Work Group of the MBA Residential Technology security risk management plan, you should not expect your plan to ransomware, and many others are all examples of malicious software |
|
Template for the Cyber Security Plan Implementation - NRCgov
program The physical protection and cyber security programs are mutually supportive of the goal of preventing acts of radiological sabotage The physical |



![48 Professional Project Plan Templates [Excel Word PDF] ᐅ 48 Professional Project Plan Templates [Excel Word PDF] ᐅ](https://cdn-images.zety.com/pages/cyber_security_resume_example_template_newcast.png)




![Cyber Security Resume Sample [Also for Entry-Level Analysts] Cyber Security Resume Sample [Also for Entry-Level Analysts]](https://saylordotorg.github.io/text_human-resource-management/section_12/53de1ffb2ac4bec86b720549678a9f68.jpg)







![48 Professional Project Plan Templates [Excel Word PDF] ᐅ 48 Professional Project Plan Templates [Excel Word PDF] ᐅ](https://images.sampletemplates.com/wp-content/uploads/2016/06/30140726/School-Safety-and-Security-Plan.jpg)

