it infrastructure security checklist
|
INFRASTRUCTURE SECURITY AWARENESS
requests suspicious activity reporting |
|
CISA MS-ISAC Ransomware Guide
Infrastructure Security. Agency (CISA) and the critical infrastructure organizations. ... The Ransomware Response Checklist which forms the other half. |
|
Federal Government Cybersecurity Incident and Vulnerability
CISA |
|
Campaign Checklist Securing Your Cyber Infrastructure 20181005
Political campaigns are facing cyber-attacks of varied sophistication. The Department of Homeland Security (DHS) has created this cybersecurity checklist to |
|
Security Checklist with VMware vRealize Cloud Management
VMware ecosystem tools delivers a secure infrastructure to organizations with multiple benefits: Security risks for inactive applications. |
|
Insider Threat Mitigation Guide
The Cybersecurity and Infrastructure Security Agency (CISA) plays an integral Insider Threat Special Interest Group “Fraud Prevention Checklist” helps. |
|
CISA Capacity Enhancement Guide. Mobile Device Cybersecurity
Facebook.com/CISA. @cisagov. CISA |
|
2.5 Bomb Threat Procedure Checklist 2020 Office Printer 8-4-20
BOMB THREAT CHECKLIST. This quick reference checklist is designed to help employees and decision makers of commercial facilities schools |
|
Digital asset SECURITY CHECKLIST
You have a FULL accounting of your entire domain name portfolio. You have an auto-renewal policy in place with your providers that is supported by credit on |
|
Campaign Checklist Securing Your Cyber Infrastructure 20181005
Political campaigns are facing cyber-attacks of varied sophistication. The Department of Homeland Security (DHS) has created this cybersecurity checklist to |
|
Audit & Penetration Testing (VAPT) Checklist - Astra Security
Infrastructure Security Audit Penetration Testing (VAPT) Checklist This document guides network administrators and network security engineers on how to |
|
Infrastructure Checklist
This Infrastructure Checklist is a quick guide to the documentation systems policies procedures and support mechanisms that nonprofit organizations |
|
Cyber security controls checklist
This is a simple checklist designed to identify and document the existence and status for a recommended basic set of cyber security controls (policies |
|
Self-guided IT Security Audit Checklist - Pathway Communications
This self-guided security audit is offered free of charge and is designed to provide guidance to help improve corporate IT security |
|
Infrastructure audit checklist - Apiko
Infrastructure checklist 1 Architecture 1 2 Code 1 3 Monitoring 2 4 Alerting 2 5 Security 2 6 Best practices 3 1 Architecture |
|
CPG Checklist - CISA
This alert is logged and stored in the relevant security or ticketing system for retroactive analysis For IT assets there is a system-enforced policy that |
|
10 POINT SECURITY CHECKLIST
Source the right test for my applications infrastructure https://www redseal net/files/PDFs/RedSeal 20UK 20B2B 20Research 20SUMMARY_July2019 pdf |
|
Network Security Audit Checklist - Pempal
Network Security Audit Checklist 1 General ? A written Network Security Policy that lists the rights and responsibilities of all staff |
|
IT Security Checklist to Protect Your Business NinjaOne
6 fév 2023 · IT security is of paramount importance when it comes to safeguarding your organization's data and technological assets Use our IT Security |
|
Network Security Checklist - Cisco
Network security might seem too complex, and tackling it might seem like too much can take a step-by-step approach as described in the checklist below, and |
|
Information Security Checklist - CAMICO
Agreements with third-party service providers should contain language indicating that: • the third-party provider will treat any client data it receives as confidential |
|
10 POINT SECURITY CHECKLIST - Bulletproofcouk
Assessment Checklist Conduct penetration testing at least once a year Source the right test for my applications infrastructure Customise testing parameters |
|
CYBER SECURITY CHECKLIST - Utahgov
Do you have policies covering laptop security (e g cable lock or secure storage)? ○ ○ 18 Do you have an emergency evacuation plan and is it current? |
|
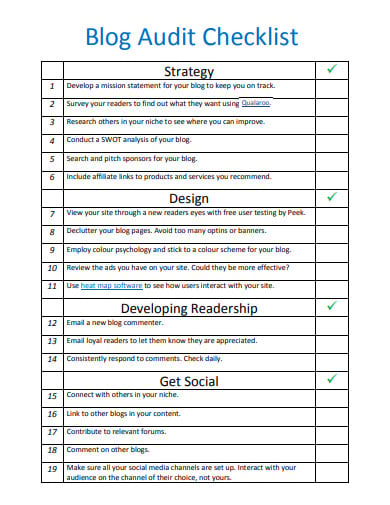
Data Governance Cloud Security Checklist at Infrastructure as a
Keywords—IaaS; security checklist; guidelines; threats; cloud computing Consumers receive essential infrastructure provided by IaaS, such as virtual |
|
Checklist for Industrial Cybersecurity - iiot-cybersec
Checklist for Industrial Cybersecurity www moxa com/security Secure Devices Secure Network Infrastructure Security Management Moxa has compiled a |
|
Protecting the Healthcare Digital Infrastructure - PHEgov
Protecting the Healthcare Digital Infrastructure: Cybersecurity Checklist Cyber Security Guidance http://www us-cert gov/reading_room/poster_1 pdf |
|
Infrastructure Checklist
This Infrastructure Checklist is a quick guide to the documentation, systems, policies, procedures, and Audit, if organization spends over $500,000 of federal |
|
The ultimate network security checklist - GFI TechTalk - GFI Software
If you're tasked with network security, either because you work on the IT security team, or perhaps you are the entire IT team by yourself, here is a simple list you |