targeted adversarial attack
|
Untargeted Targeted and Universal Adversarial Attacks and
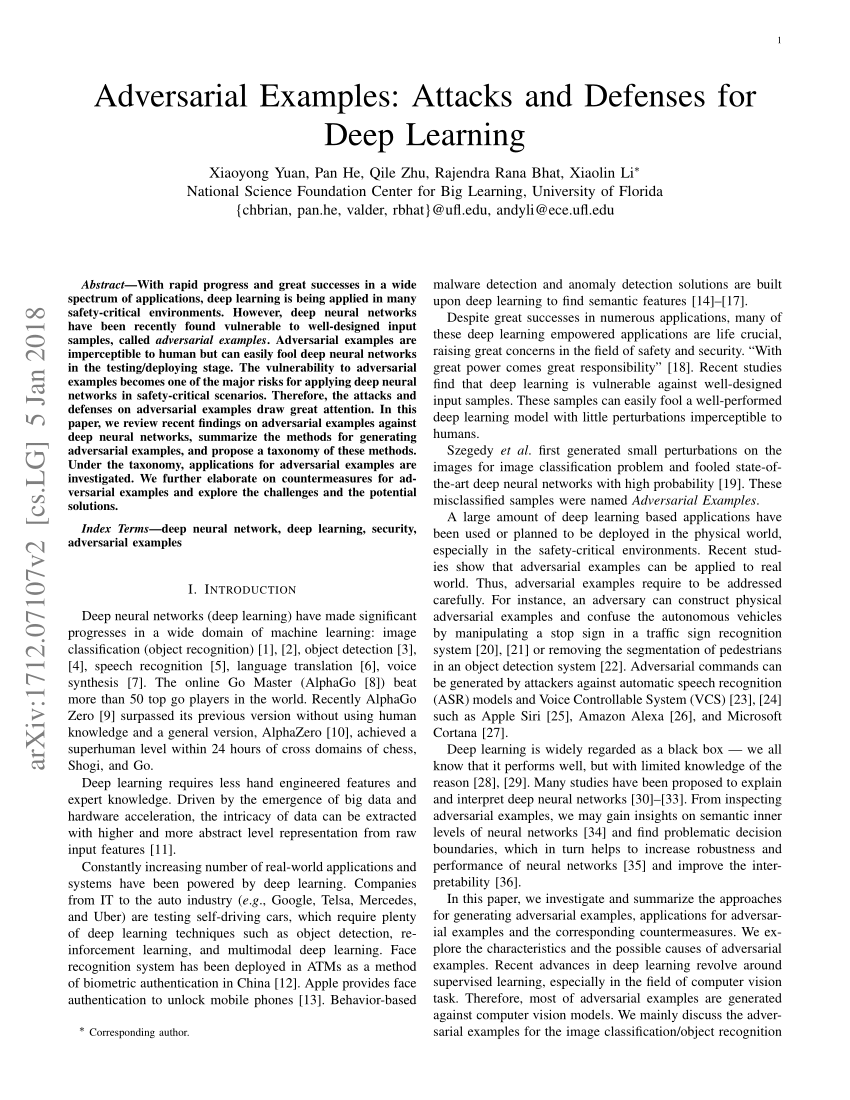
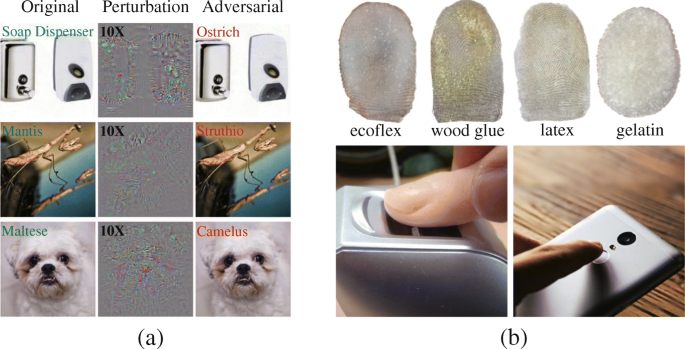
1 Example of targeted adversarial attack on 'Large Kitchen Appliances' dataset by adding imperceptible noise. • Untargeted attacks are the attacks where the |
|
Chapter 3 Adversarial Attack
Attacks of this type is known as the untargeted attack. For the time being let us focus on targeted attack first. There are various approaches to move a data |
|
Targeted Mismatch Adversarial Attack: Query With a Flower to
Similarly to image classification adversarial attacks have been proposed in the domain of image retrieval too. An non-targeted attack attempts to generate an |
|
Miss the Point: Targeted Adversarial Attack on Multiple Landmark
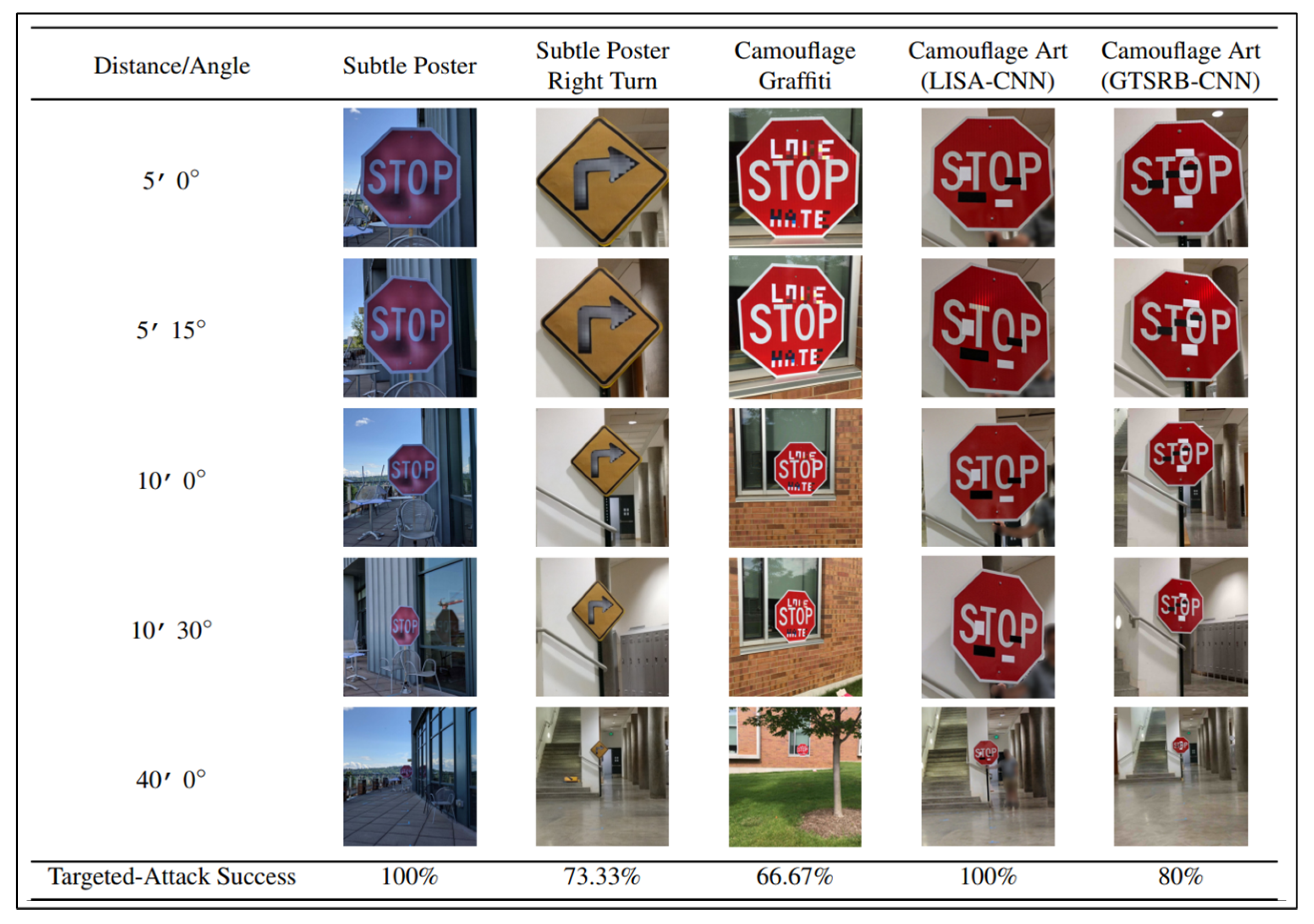
Adversarial attacks against CNN models become a real threat not only in classification tasks but also in segmentation and localization [21]. The dense adversary |
|
Targeted Adversarial Training for Natural Language Understanding
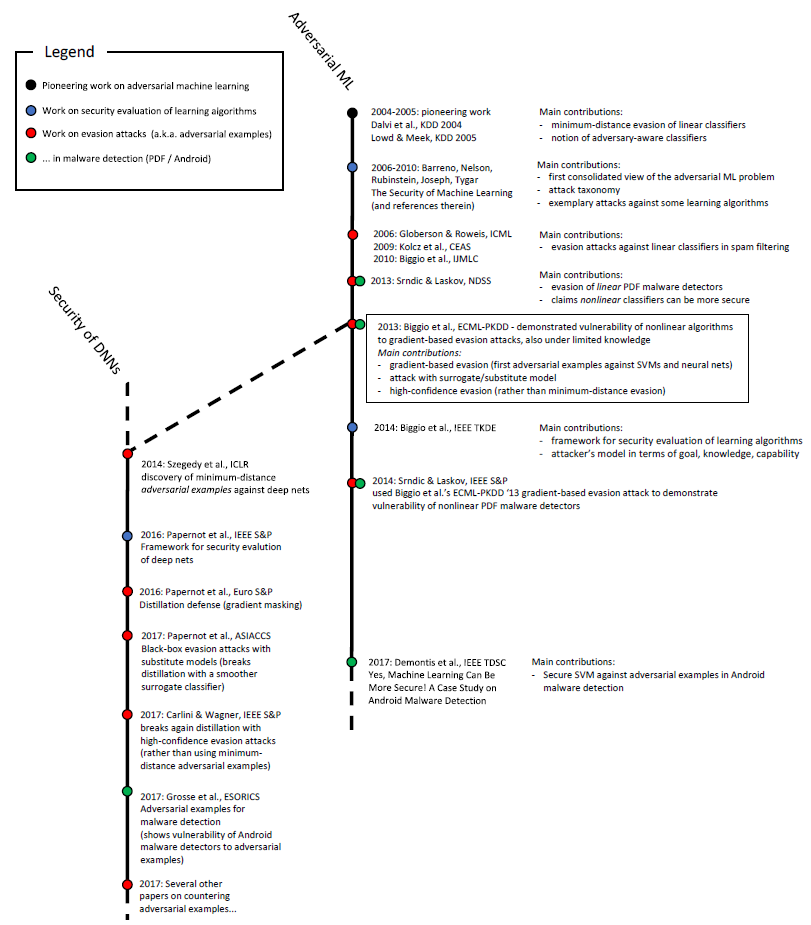
2017) most adversarial training approaches adopt non-targeted attacks |
|
Targeted Adversarial Perturbations for Monocular Depth Prediction
[40] studied non-targeted perturbations for stereo and [35] used patch attacks for optical flow. [28] examined universal perturbations in a data-free setting |
|
TOG: Targeted Adversarial Objectness Gradient Attacks on Real
9. 4. 2020 TOG: Targeted Adversarial Objectness Gradient Attacks on Real-time Object Detection Systems?. Ka-Ho Chow Ling Liu |
|
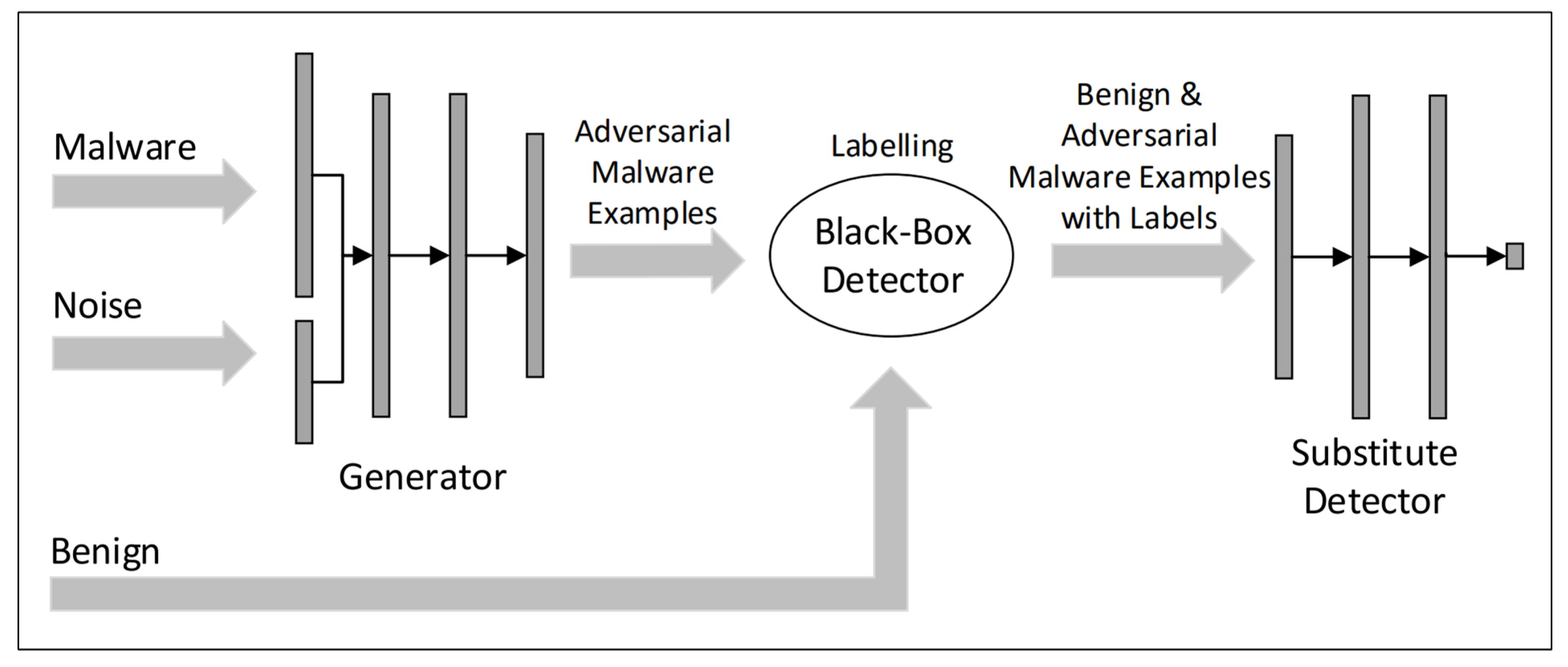
Black-box Adversarial Attacks with Limited Queries and Information
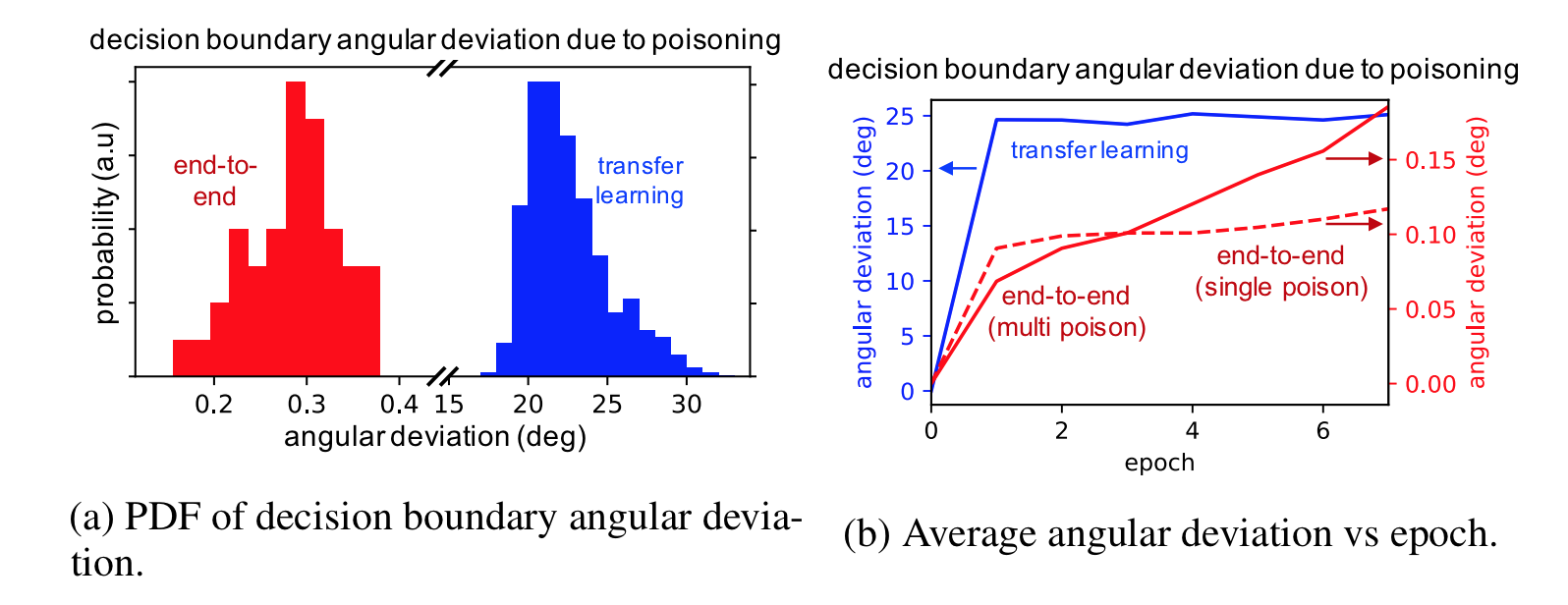
Recent works note that adversarial examples for substitute networks do not always transfer to the target model especially when con- ducting targeted attacks ( |
|
Towards Transferable Targeted Attack
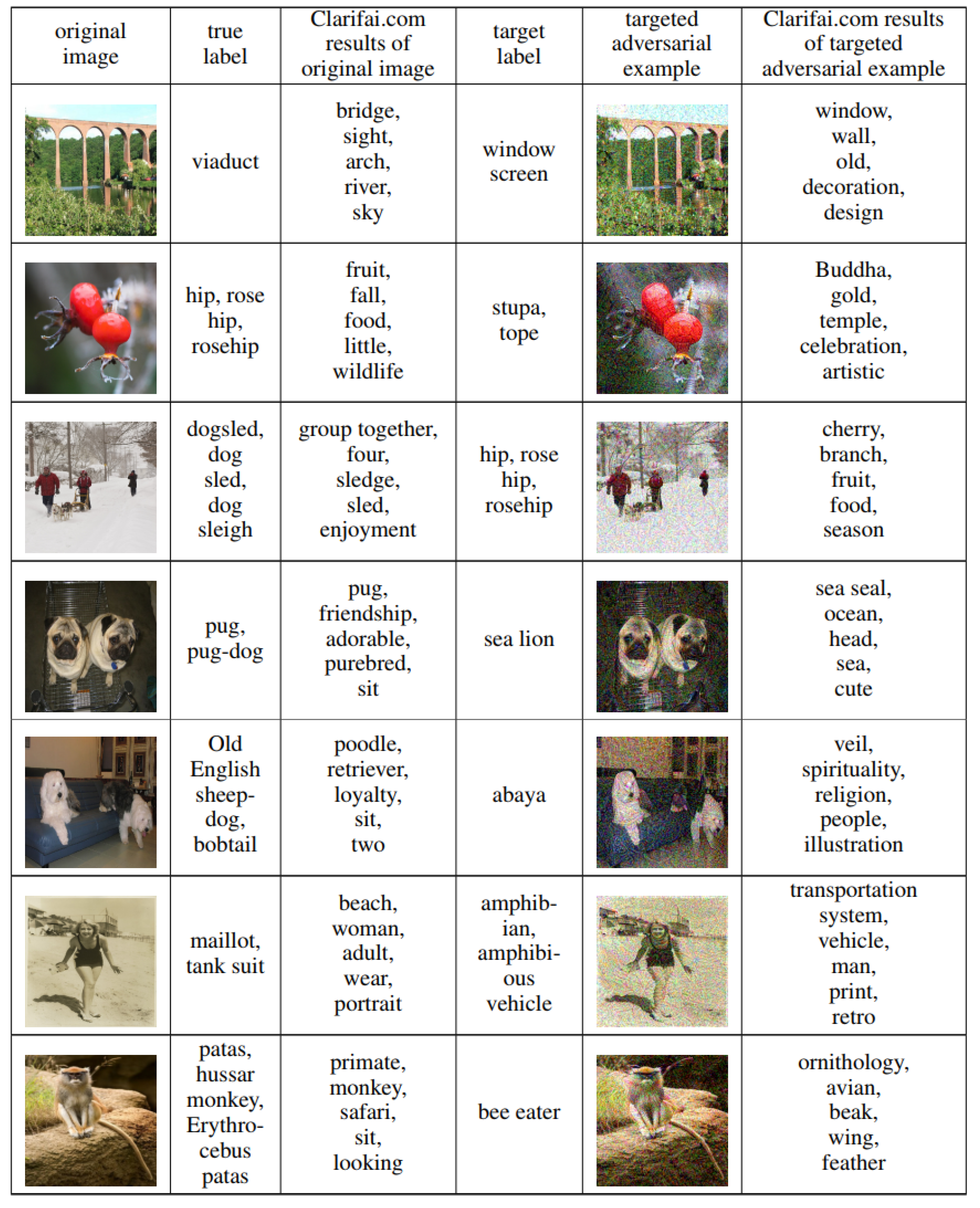
An intriguing property of adversarial examples is their transferability which suggests that black-box attacks are feasible in real-world applications. Previous |
|
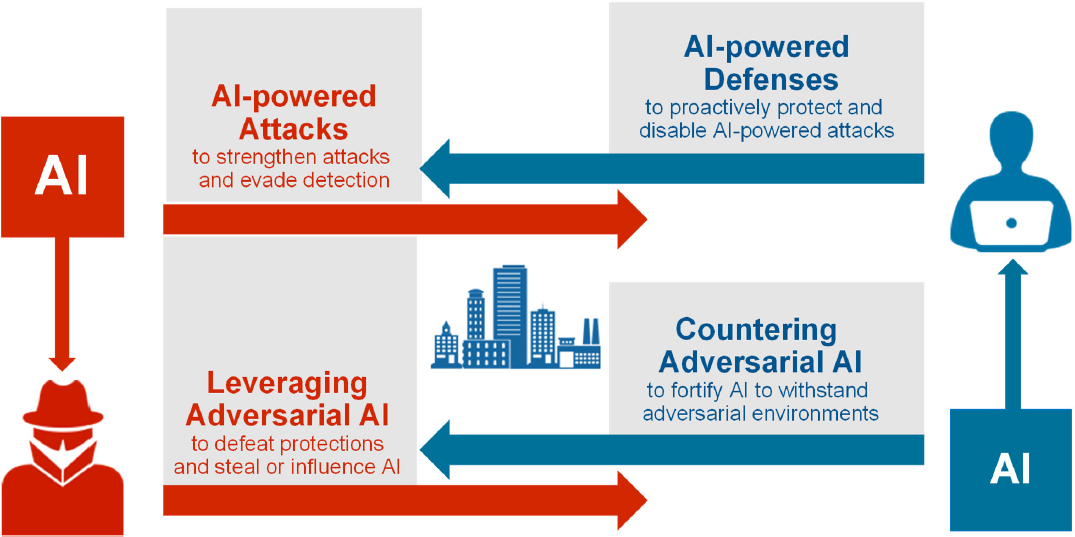
Defenses Against Adversarial Attacks - University of Idaho
Targeted Adversarial Attack The goal of the targeted attack is to slightly modify a source image in a way that the image will be classified as specified target class by a generally unknown machine learning classifier 4 Proactive defense: The defenses are constantly looking for potential attackers |
|
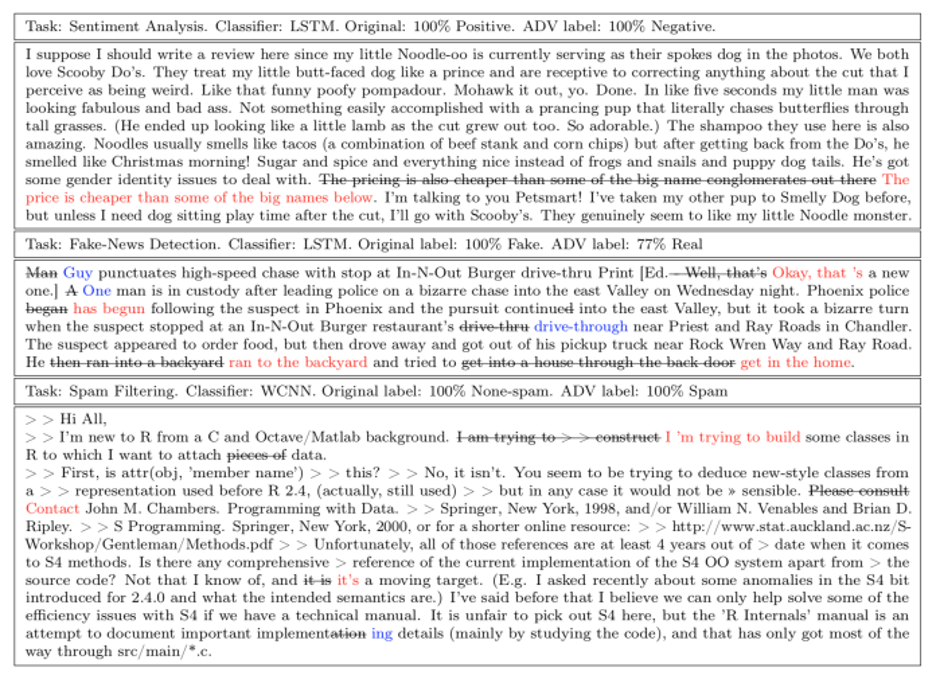
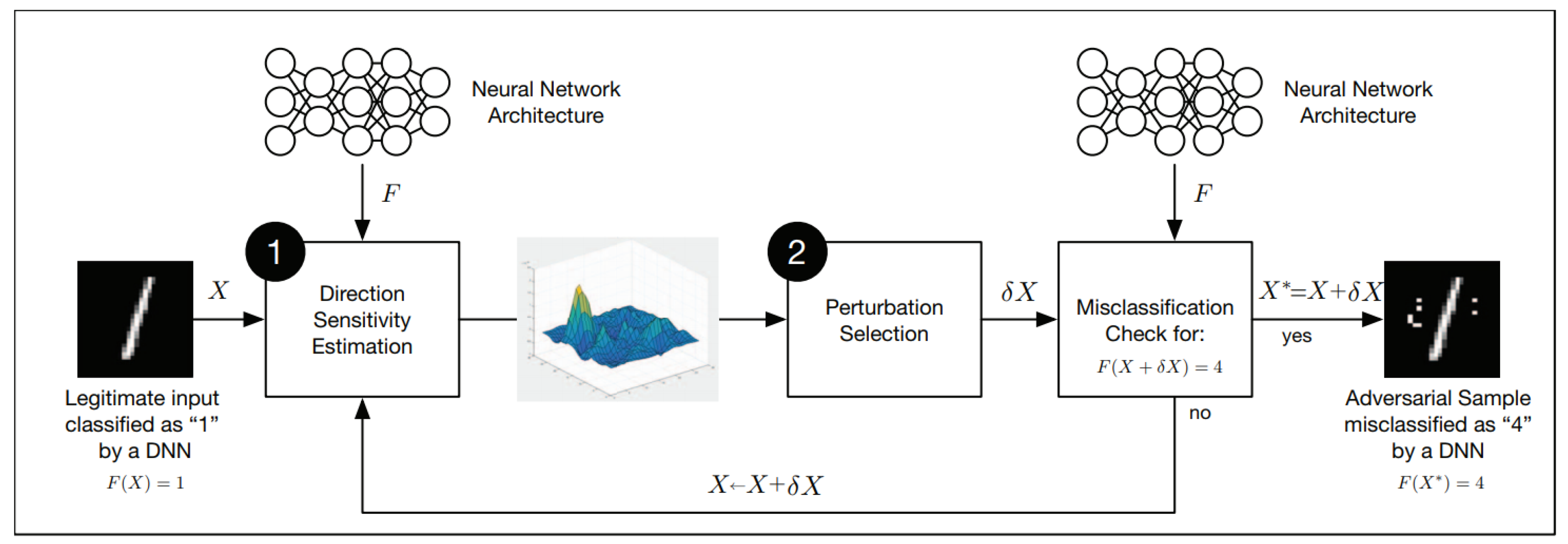
Chapter 3 Adversarial Attack - Purdue University College of
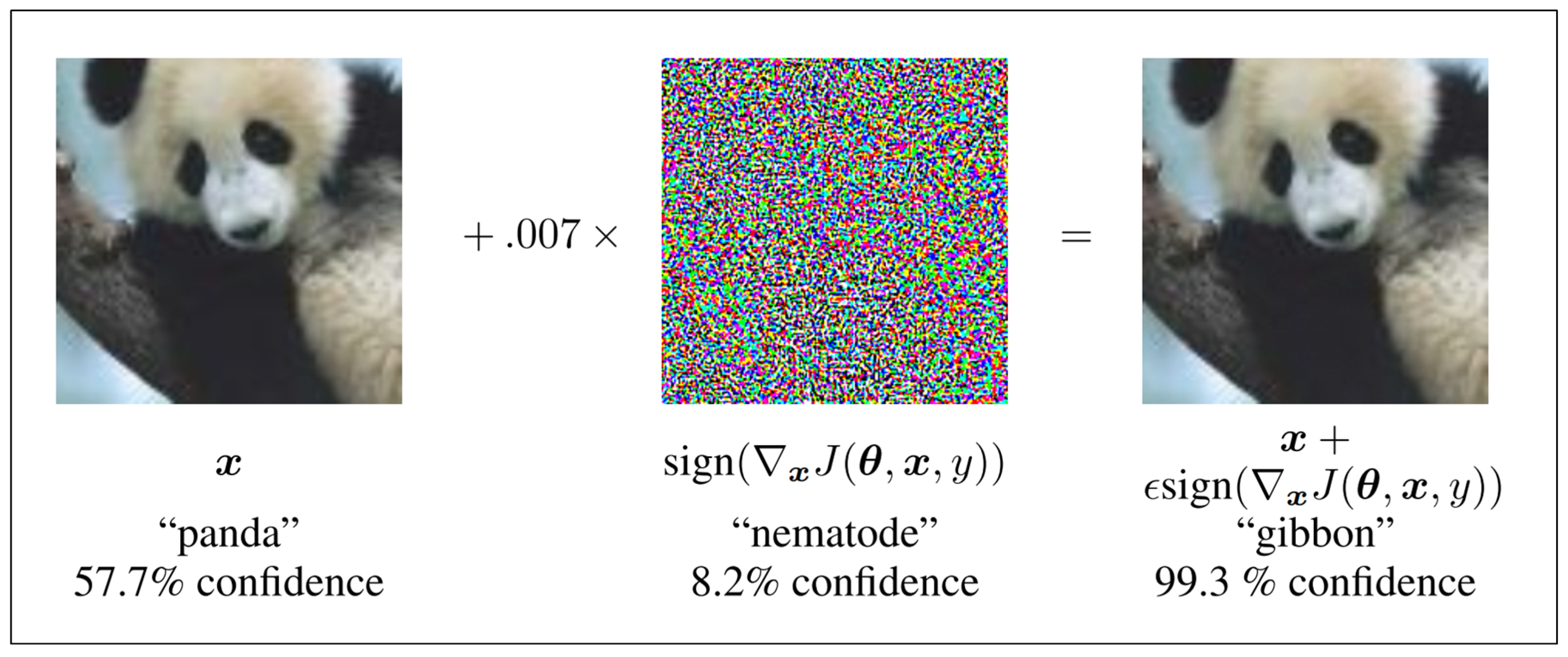
Adversarial attack is an malicious attempt to perturb a data point x0 2Rdto anotherpointx2Rdsuch that xbelongs to certaintargetadversarial class For example if x0is feature vector of acatimage by adversarial attack we meant to create another featurevector xwhich will be classi er as adog(or another class speci ed by the attacker) |
|
Searches related to targeted adversarial attack PDF
targeted adversarial attacks to protect against facial image manipulations As powerful face image manipulation tools became easier to use and more widely available many efforts to detect image manipulations were initiated by the research community [13] This has led to the task of automatically detecting |
What is universal adversarial attack?
In contrast, universal adversarial attack calculates a special imperceptible noise which can be added to any sample of the given dataset so that, the deep learning model is forced to predict a wrong class. To the best of our knowledge these targeted and universal attacks on time series data have not been studied in any of the previous works.
Is the minimally distorted adversarial example more efficient?
This procedure is more ef?cient for ?nding the minimally distorted adversarial example. The authors claim their attack is one of the strongest attacks, breaking many defense strategies which were shown to be successful.
What is adversarial detection?
(c) Adversary Detection (Carlini & Wagner,2017a;Xu et al.,2017): the approaches attempt to check whether a sample is benign or adversarial before feeding it to the deep learning models. It can be seen as a method of guarding against adversarial examples.
Do image processing tools protect against adversarial examples?
The work in (Guo et al.,2017) studies a number of image processing tools, such as image cropping, compressing or total-variance minimization, to de- termine whether these techniques help to protect the model against adversarial examples.
|
Targeted Mismatch Adversarial Attack: Query - CVF Open Access
Similarly to image classification, adversarial attacks have been proposed in the domain of image retrieval too An non-targeted attack attempts to generate an |
|
Adversarial examples in Deep Neural Networks
Types of attack According to the attacker's goal: Non-targeted attacks: attacker tries to fool a classifier to get any incorrect clas Targeted attacks: attacker tries to |
|
Imperceptible, Robust, and Targeted Adversarial Examples for
for speech recognition systems targeting arbitrary (multi- word) sentences However, this attack was neither effective over-the-air, nor was the adversarial |
|
Chapter 3 Adversarial Attack - Purdue Engineering
In some scenarios, the goal may not be to push x0 to a specific target class Ct, but just push it away from its original class Ci Attacks of this type is known as the |
|
Multi-targeted Adversarial Example in Evasion Attack - IEEE Xplore
Therefore, in this paper, we propose a multi-targeted adversarial example that attacks multiple models within each target class with a single modified image To |
|
Adversarial Attacks at Prediction - Sites/USP
– Make the target model to misclassify by predicting the adversarial example as a class other than the original class Page 8 8/1/19 8 Targeted Attack |
|
ROBUSTNESS OF ADVERSARIAL ATTACKS IN SOUND - CORE
Similarly, most of the work on defenses against adversarial at- tacks is focused on automatic speech recognition Research has shown that mp3 compression, |
![PDF] Multi-Targeted Adversarial Example in Evasion Attack on Deep PDF] Multi-Targeted Adversarial Example in Evasion Attack on Deep](https://i1.rgstatic.net/publication/333063425_Deep_adversarial_attack_on_target_detection_systems/links/5d4dd51fa6fdcc370a89cab7/largepreview.png)






![PDF] Multi-Targeted Adversarial Example in Evasion Attack on Deep PDF] Multi-Targeted Adversarial Example in Evasion Attack on Deep](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs11042-020-09604-z/MediaObjects/11042_2020_9604_Fig1_HTML.png)













![PDF] Miss the Point: Targeted Adversarial Attack on Multiple PDF] Miss the Point: Targeted Adversarial Attack on Multiple](https://raw.githubusercontent.com/as791/Adversarial-Example-Attack-and-Defense/master/images/fgsm-attack.png)